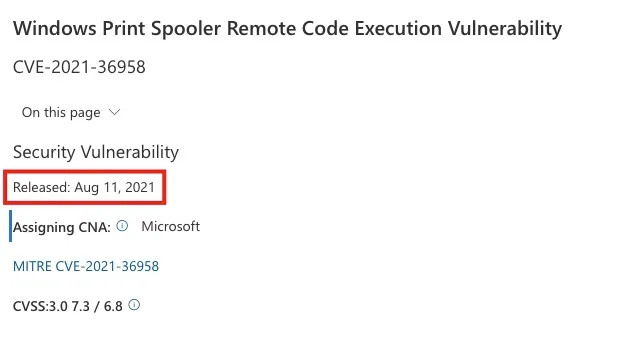
Microsoft has issued an advisory for another zero-day Windows print spooler vulnerability tracked as CVE-2021-36958 that allows local attackers to gain SYSTEM privileges on a computer. As stated by Microsoft, an attacker who successfully exploits this vulnerability could run arbitrary code with SYSTEM privileges.
I you wish to have more detailed information on the development of this vulnerability, when it was first discovered, its workaround and patches released so far, please visit the following links.
Unlike the previous exploits, this vulnerability affects for the Windows print spooler, Windows print drivers, and Windows Point and Print. For a detailed guide, please refer to this link.
Here is a link to the video (Twitter trend) as discovered by Benjamin Delpy.
How do you mitigate this issue? There isn’t a patch (update) as at the time of this writing. The good thing is, there is always a workaround.
– You can disable the Print Spooler service or allow your device to install printers from authorized servers. Below are the steps to perform both operations.
Disable the Print Spooler Service: If disabling the Print Spooler service is appropriate for your enterprise, use the following PowerShell commands.
– First, determine if the Print Spooler service is running via services.msc or PowerShell. If you will be using PowerShell, run the command below.
Get-Service -Name Spooler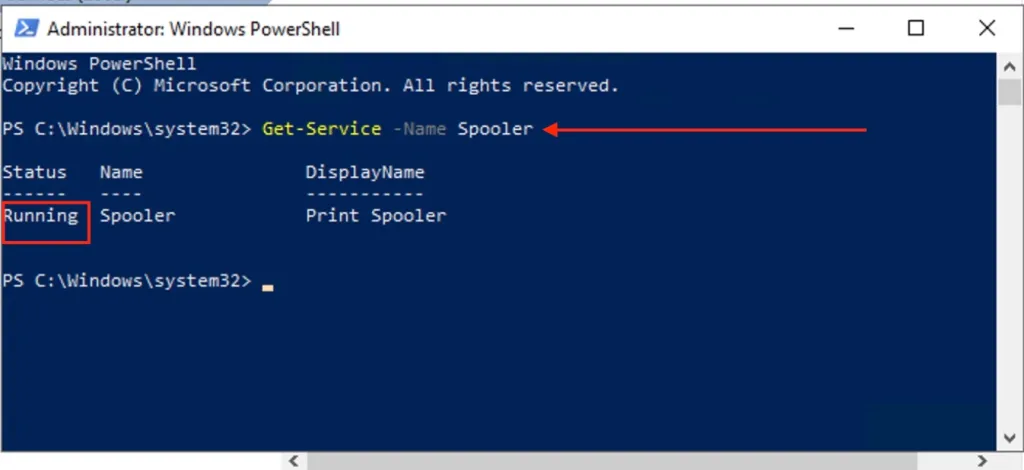
To disable the print spooler, please run the following command below
Stop-Service -Name Spooler -Force
Set-Service -Name Spooler -StartupType Disabled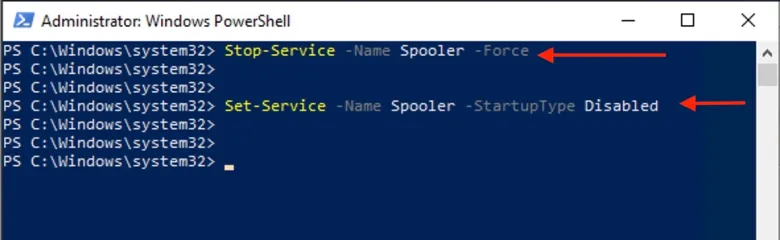
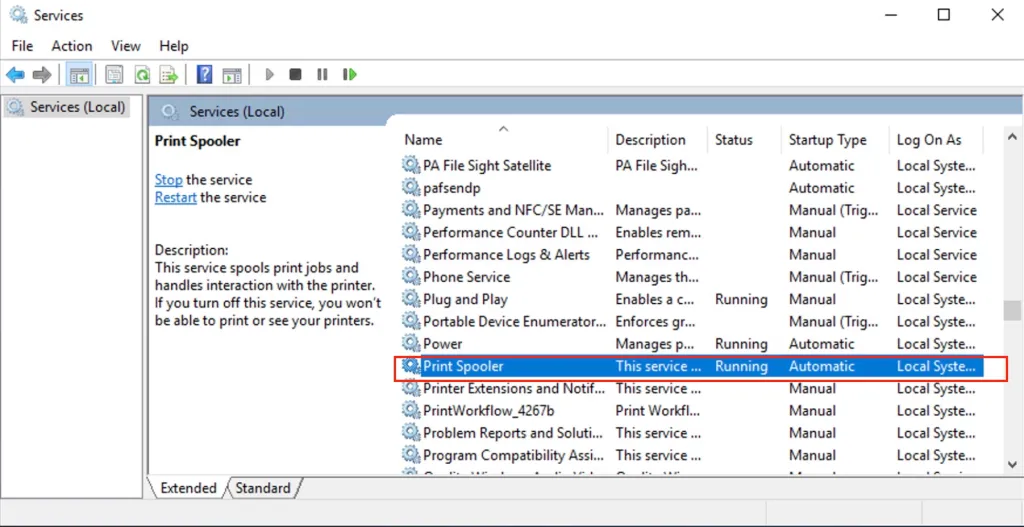
To disable the Print Spooler Service via services.msc, please follow the steps below.
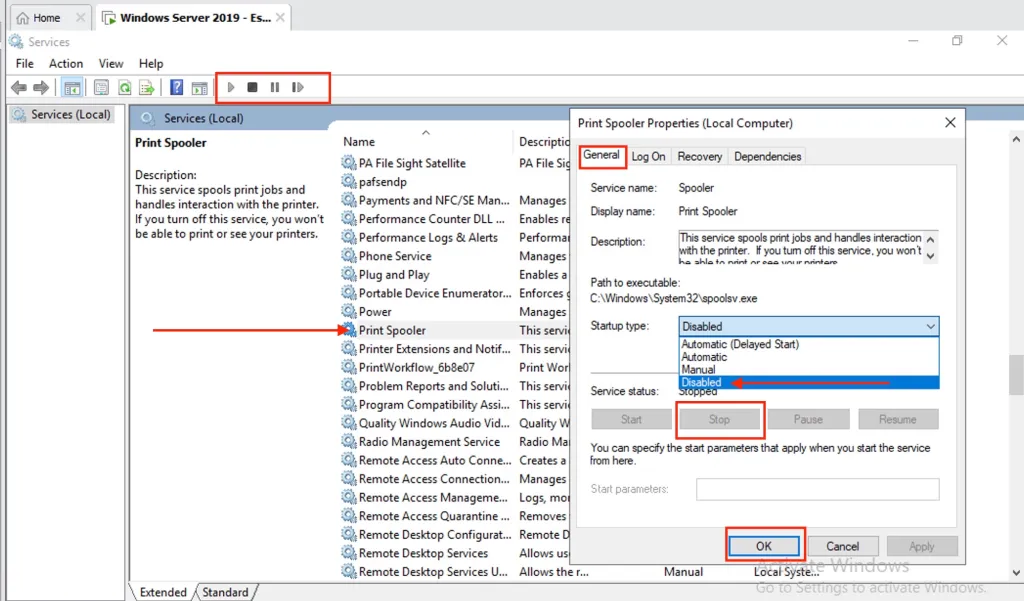
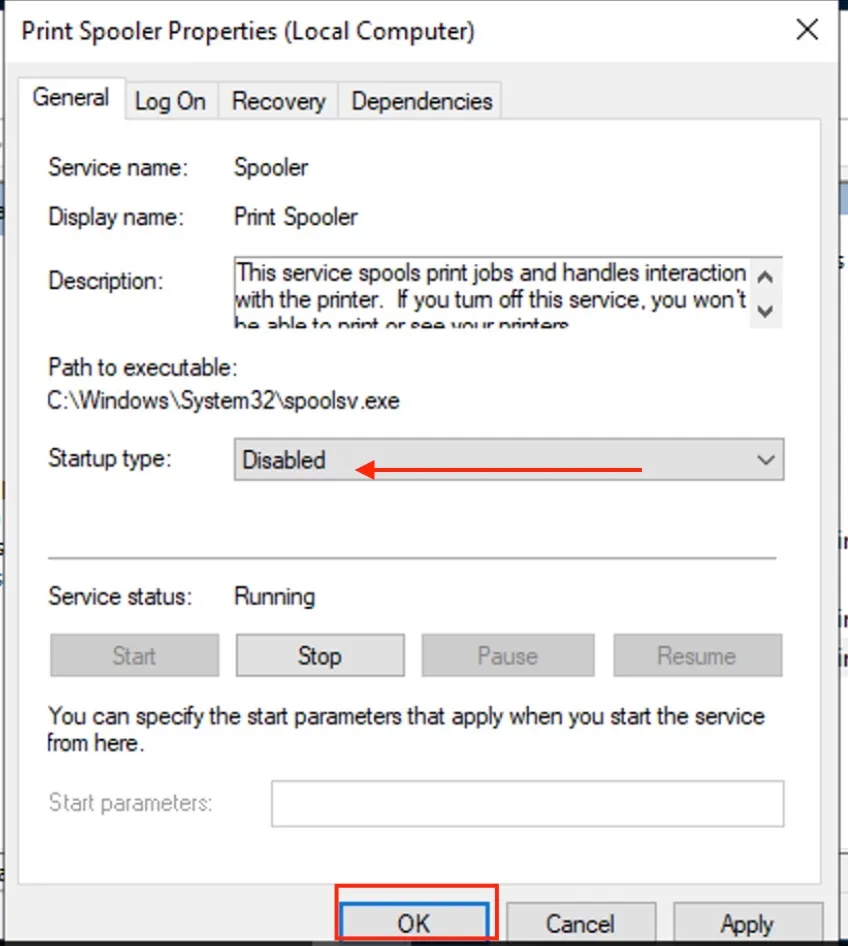
Impact of workaround Stopping and disabling the Print Spooler service disables the ability to print both locally and remotely.If you wish to start this in the future, kindly launch Windows Services and right-click on the Print Spooler service, and select properties.
– Select a startup type and click on start.
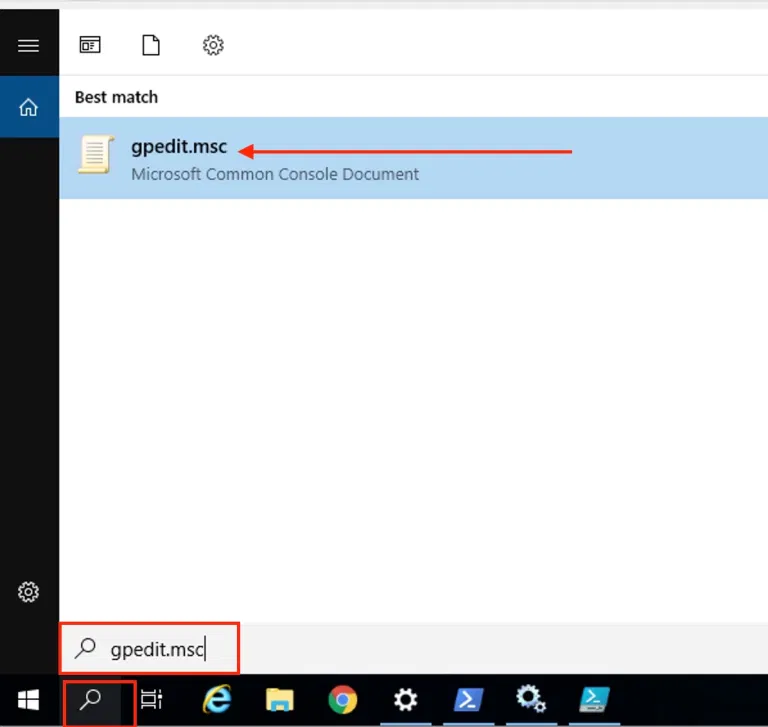
Enable your device to download drivers from Authorized Servers Only: You can also configure the settings via Local Group Policy as shown below. You may want to see this guide before proceeding: What is GPO and how can it be launched in Windows.
– To launch the Local Group Policy console, open the run dialog box, search for “gpedit.msc” or from Windows Search, as shown below.
This will open up the Local Group Policy Editor as shown below. Navigate through the following as described.
– Expand the User Configuration, click on the Administrative Templates, and then expand the Control Panel node.
– Select Printers and click on Package Point and Print — Approved Servers.
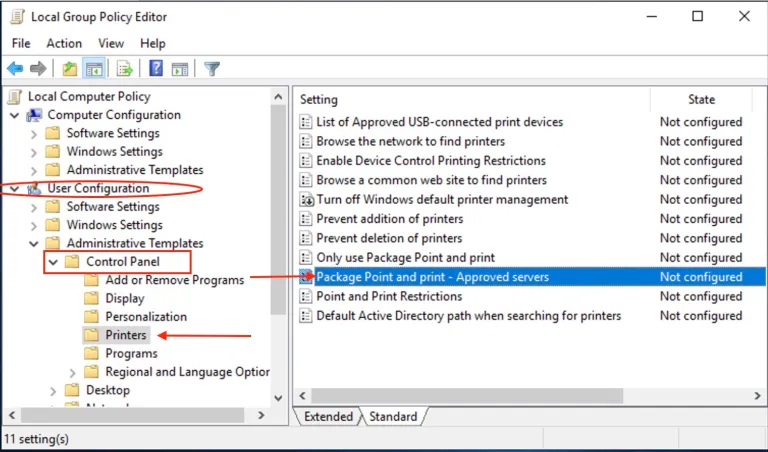
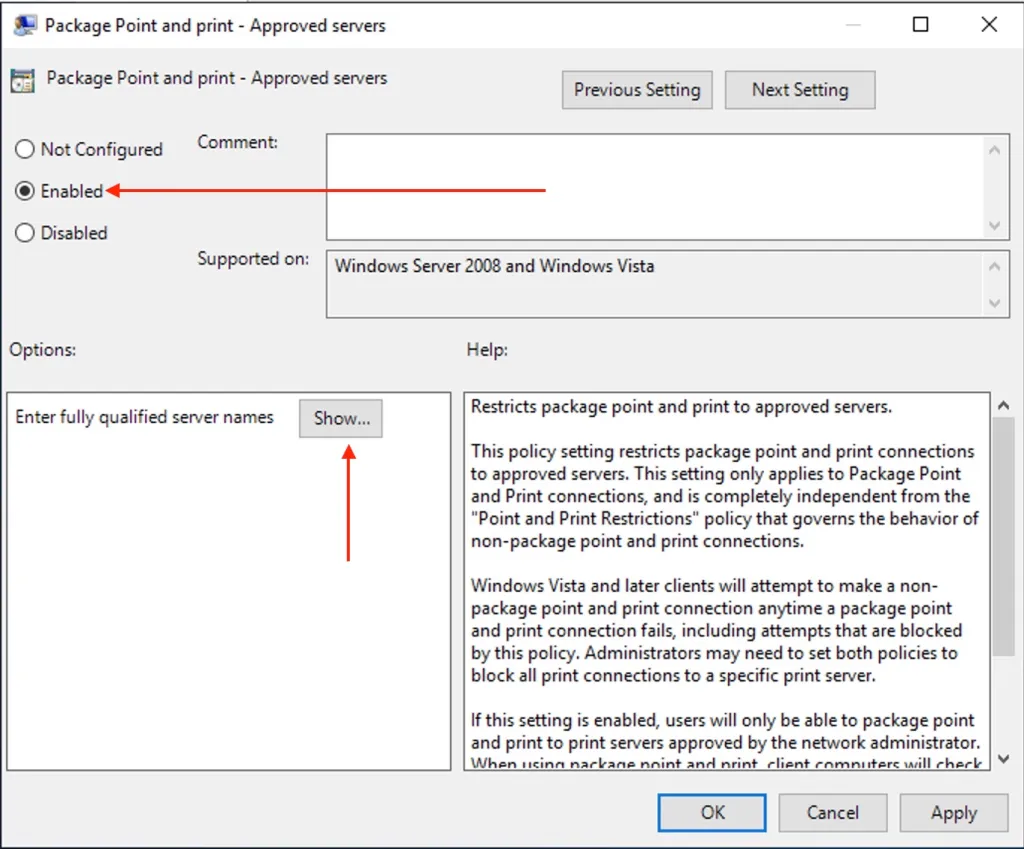
This will open the Package Point and Print—Approved Servers settings window.
– Click on Enabled
– Click on show,
– In the list content window, enter the FQDN of the servers as shown in the image below.
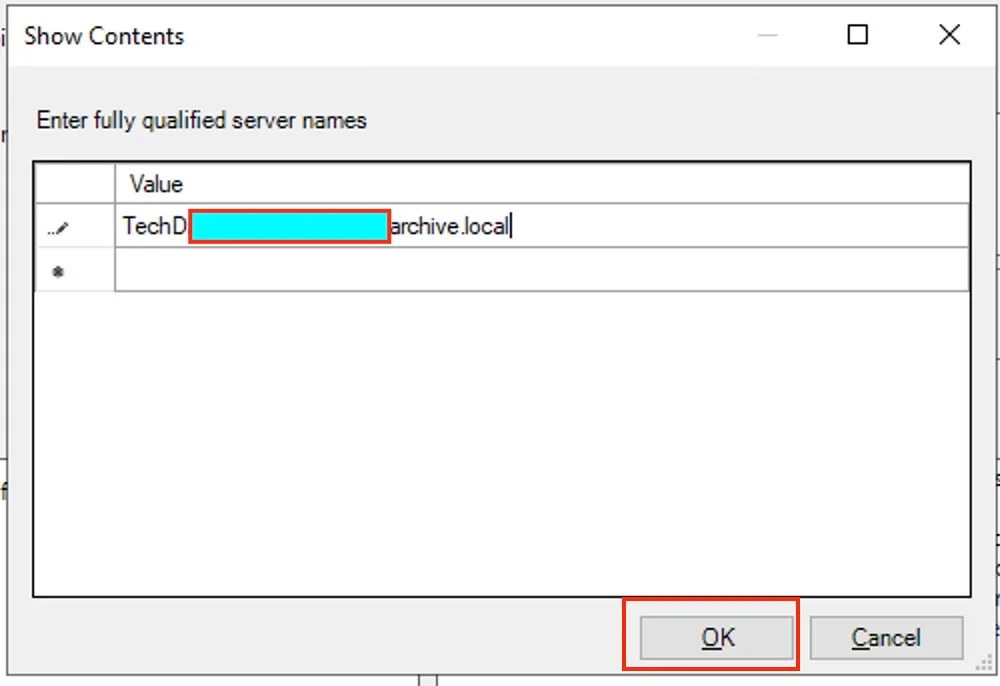
When you are done, click on Ok.
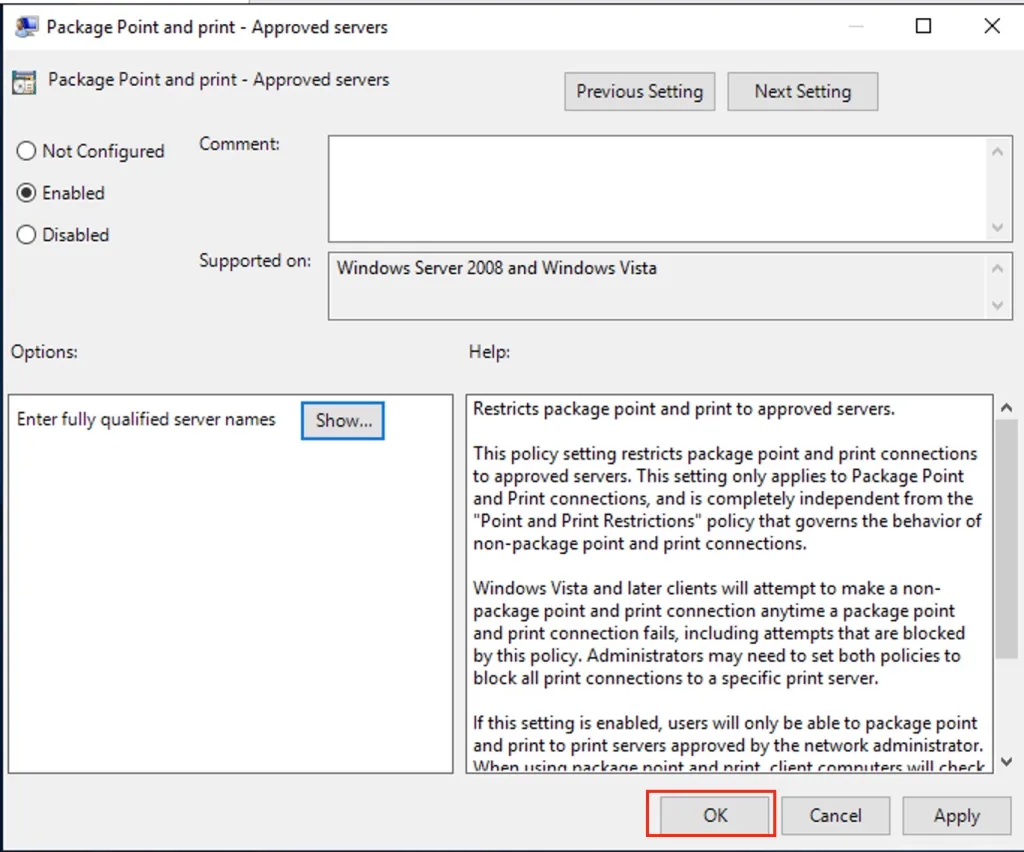
Until the patch is released, this workaround should be able to protect you unless the threat actor can take over an authorized print server with malicious drivers.
If you wish the policy to take effect immediately without waiting for the default settings, please run any of the following commands discussed in this hyperlink: GPUpdate and GPUpdate /force. Group policy on Windows 10 periodically refreshes the Registry at certain intervals to keep the Registry values in check at all times which is an interval of 90 minutes.
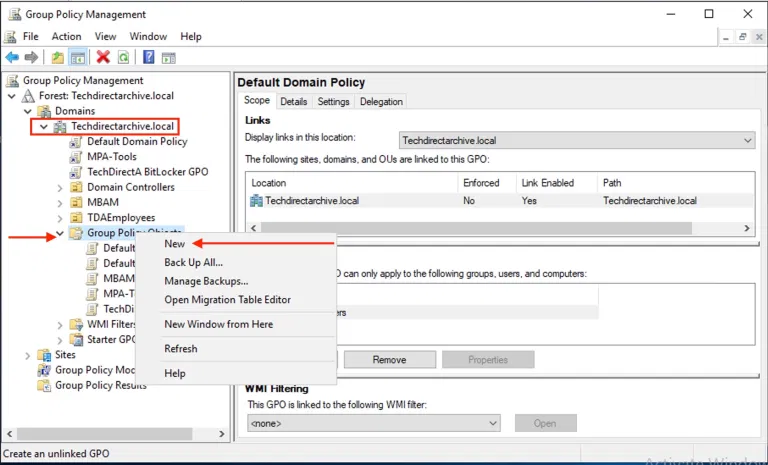
You may want to roll this setting domain-wide to your internal systems. To launch Group Policy from the Domain controller,
– Launch the Server Manager. (Note: you can also use the Windows Administrative Tools for this).
– Under Tool,
– Search for Group Policy Management. This will open up the Group Policy Management Console. You can also use the “Advanced Group Policy Management (AGPM)”.
I hope you found this blog post helpful.

