Greetings, everyone! Today we'll delve into the art of identifying basic file Indicators of Compromise (IoCs), crafting YARA rules to sniff out malicious actors, and seamlessly integrating these rules into Veeam Backup & Replication to safeguard our backups against potential malware threats. But before we dive in, let's take a moment to understand YARA and what its for.
YARA
YARA is an open-source malware classification tool used to identify and classify malware or suspicious files based on its signatures or rules. It is a powerful and flexible tool that allows users to create rules matching their organization’s needs or targeting specific threats. Moreover, YARA rules are like a piece of programming language, they work by defining a number of variables that contain patterns found in a sample of malware. If some or all of the conditions are met, depending on the rule, then it can be used to successfully identify a piece of malware.
Indicators of Compromise (IoCS)
Suppose one day a user notices a suspicious document on their desktop named Susfile1.txt. Instead of opening it and potentially spreading malware, we should analyze the file to identify any indicators of compromise (IoCs).
In its simplest form, we first examine the file's properties. The initial indicators of compromise (IoCs) we get are the name, extension, file path, and size in bytes.
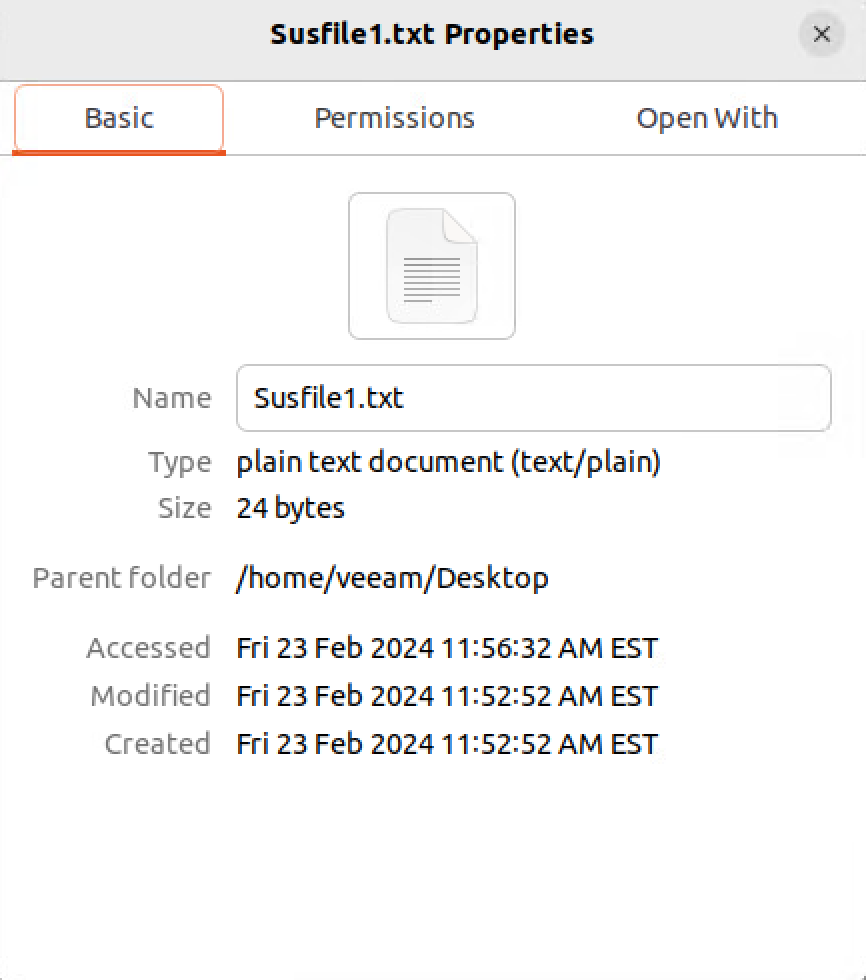
So far, basic info from properties:
- File Name: Susfile1.txt
- File Path: /home/veeam/Desktop
- File Size: 24 Bytes
That’s not really a whole to work with.. so next step is to run strings on the file. Strings is a tool that can gather collections of characters that produce human readable text. 9 times out of 10, you will get a ton of gibberish characters. As a good habit, let’s pipe the output into a text file.
strings Susfile1.txt > Susflie1strings.txt
Once we have the output, we can cat the text file to view the output data.
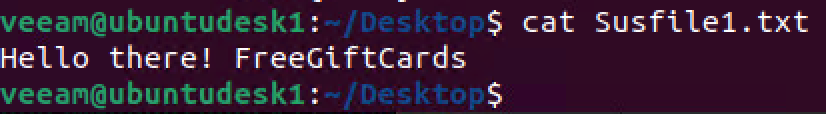
Now, we can add the additional information collected to our list:
- File Name: Susfile1.txt
- File Path: /home/veeam/Desktop
- File Size: 24 Bytes
- Strings: “Hello there! FreeGfitCards”
The next step to take is to collect the file hashes… We can do that by running the following commands:
md5sum Susfile1.txt
sha1sum Susfile1.txt
sha256sum Susfile1.txt
Our list of information is growing…
- File Name: Susfile1.txt
- File Path: /home/veeam/Desktop
- File Size: 24 Bytes
- Strings: “Hello there! FreeGiftCards”
- MD5 Hash: f1bc52b1c4da8b1d9dbe44bf41697d9d
- SHA1 Hash: acf20e2e687005925149527e979220d21ded5696
- SHA256 Hash: a6592f3b045c0d897899a25b3b0b10a4c8444e28764cfcf2717dee1b67d3ecb
Creating the YARA
Now that we have some information from this suspicious file, let’s start making a YARA rule. Afterwards we can use YARA to hunt for any additional files that meet our strings and conditions.
You can use any text editor based on your preference / OS… I am using nano on Ubuntu.
nano veeam.yara
There are some basic concepts to follow when creating a YARA rule:
- You have to give it a name
- You can use metadata (author, description, hash)
- You can use Strings (these are specific text / characters / expressions you want to search for)
- You have to use conditions ( combination of strings, file size, Hex or text)
rule veeam
{
meta:
author = "Andy"
date = "2024"
description = "This is a veeam yara demo."
reference = "Blank"
md5hash = "f1bc52b1c4da8b1d9dbe44bf41697d9d"
sha1hash = "acf20e2e687005925149527e979220d21ded5696"
sha256hash = "a6592f3b045c0bd897899a25b3b0b10a4c8444e28764cfcf2717dee1b67d3ecb"
strings:
$s1 = "Hello there!"
$s2 = "FreeGiftCards"
condition:
($s1 or $s2) and filesize < 20KB
}
Let’s now run the YARA rule with the command below. This will scan the system and look for files that share the similar information as defined in your strings and conditions.
sudo yara -m -s -r veeam.yara ~/ 2>/dev/null
(-m feeds the YARA rule file, -s shows the strings on which YARA detected, -r searches recursively)
Depending on what files get identified by the YARA, we could then choose to collect the IoCs for new identified files and then update the YARA rule and run it again if need be.
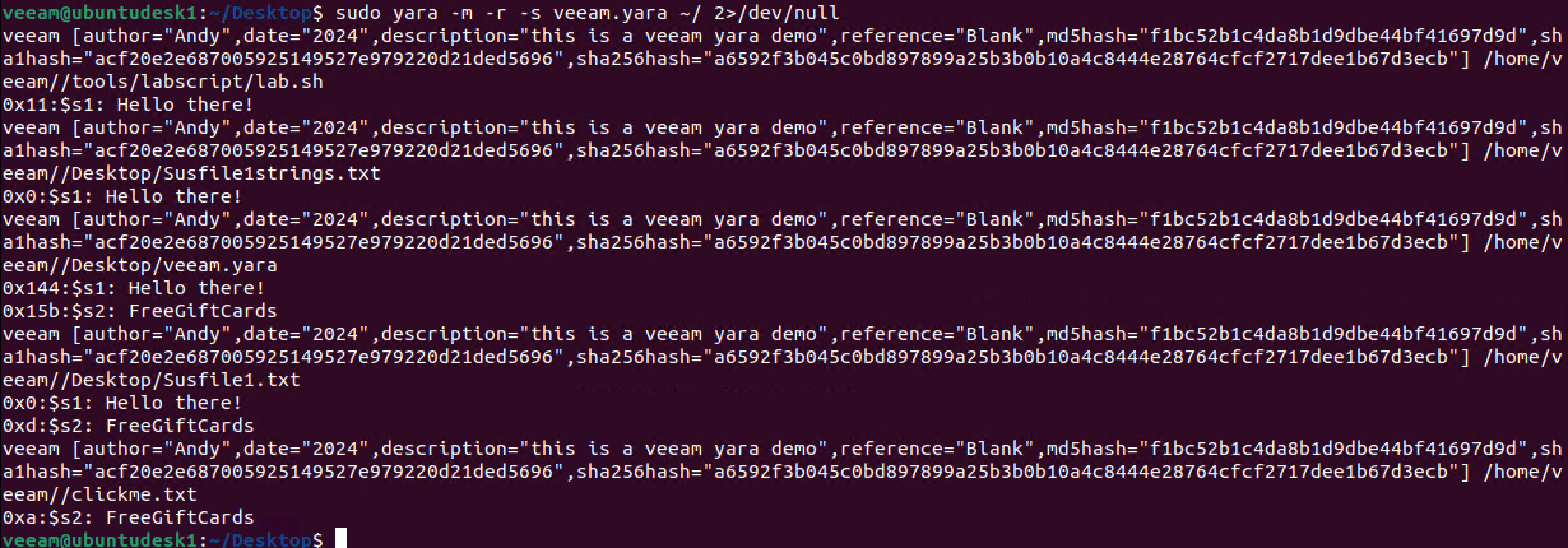
Looks like a new file was identified…. clickme.txt
Let’s take a look at that file and gather its IoCs….
- File Name: clickme.txt
- File Path: /home/veeam/Desktop
- File Size: 38 Bytes
- Strings: “bitcoin.. FreeGiftCards NFT”
- MD5 Hash: e10edced670747f31ce544a5ec39b4eb
- SHA1 Hash: d6a51843f65d032abfb2ec500ce11f32ea72e39d
- SHA256 Hash: 0833077daa6d59306178a61efde6063cbe45eb2d107d4c28649ce579b70826f
We can now go back to our YARA rule and update it to include the additional strings & to change the condition:
rule veeam
{
meta:
author = "Andy"
date = "2024"
description = "This is a veeam yara demo."
reference = "Blank"
md5hash1 = "f1bc52b1c4da8b1d9dbe44bf41697d9d"
md5hash2 = "e10edced670747f31ce544a5ec39b4eb"
strings:
$s1 = "Hello there!"
$s2 = "FreeGiftCards"
$s3 = "bitcoin"
$s4 = "NFT"
condition:
(1 of them) and filesize < 20KB
}
At this point i think you can understand the general concepts of YARA and its uses.
- Collect the IoCs of your potential malicious file
- Create a YARA rule to scan an entire system and look for other instances of them.
- Rinse. Repeat to your liking.
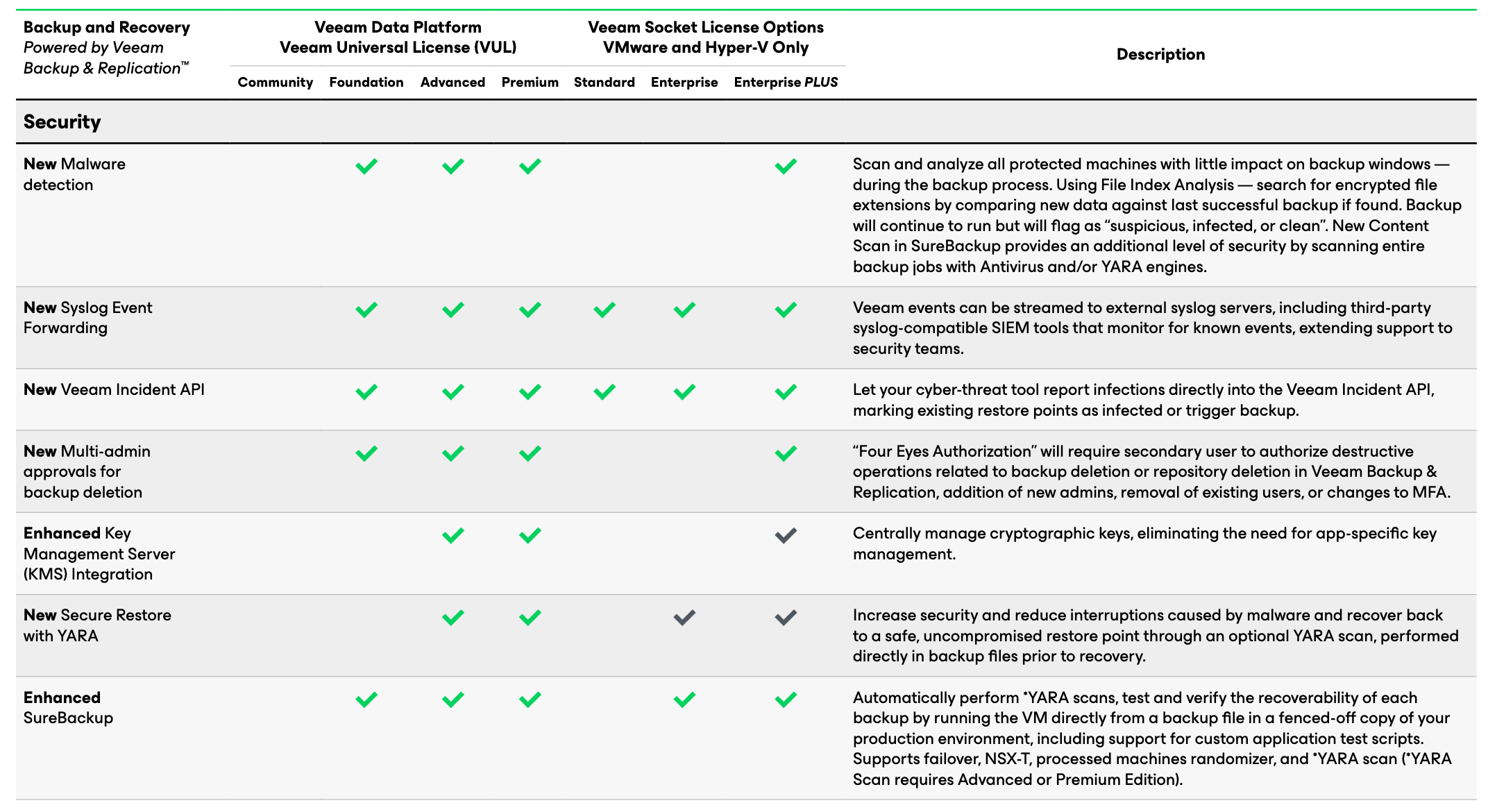
Veeam Backup & Replication & YARA
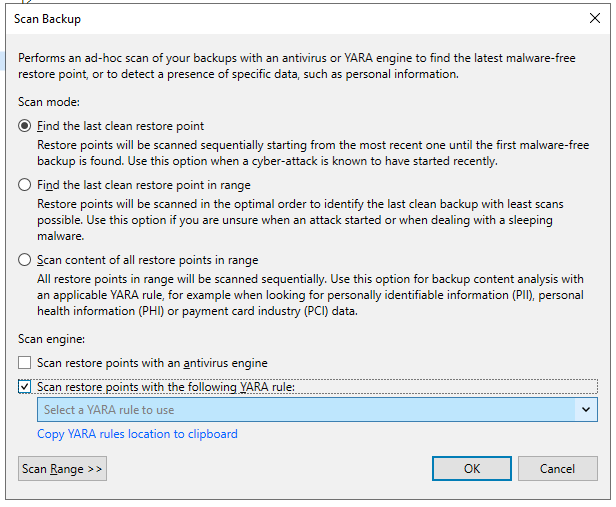
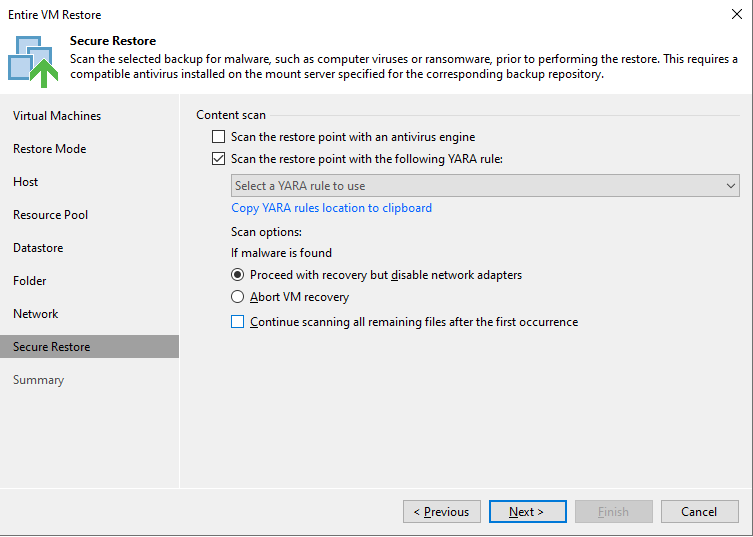
Now that we have a YARA rule, we can use it in Veeam Backup & Replication to search through our existing backups for any malicious files. To do this, copy the YARA rule to the specified folder on our VBR server. (If you're unsure where that is, refer to the link provided. The image below will copy the location to your clipboard.) There are two methods to use a YARA rule within Veeam Backup & Replication…. Let’s go over them now.
YARA Scan for Scan Backup
This option allows you to run YARA rules on existing restore points. For example, find the last clean restore point or to analyze content for specific information or sensitive data.
YARA Scan for Secure Restore
This option allows you to run YARA rule when performing a restore of a workload. Much like Secure Restore with Antivirus options, you have several options on how you would like to proceed if something was found.
Viewing YARA Scan Results
The results of the YARA scan can be viewed in the Statistics section of each scan Job.
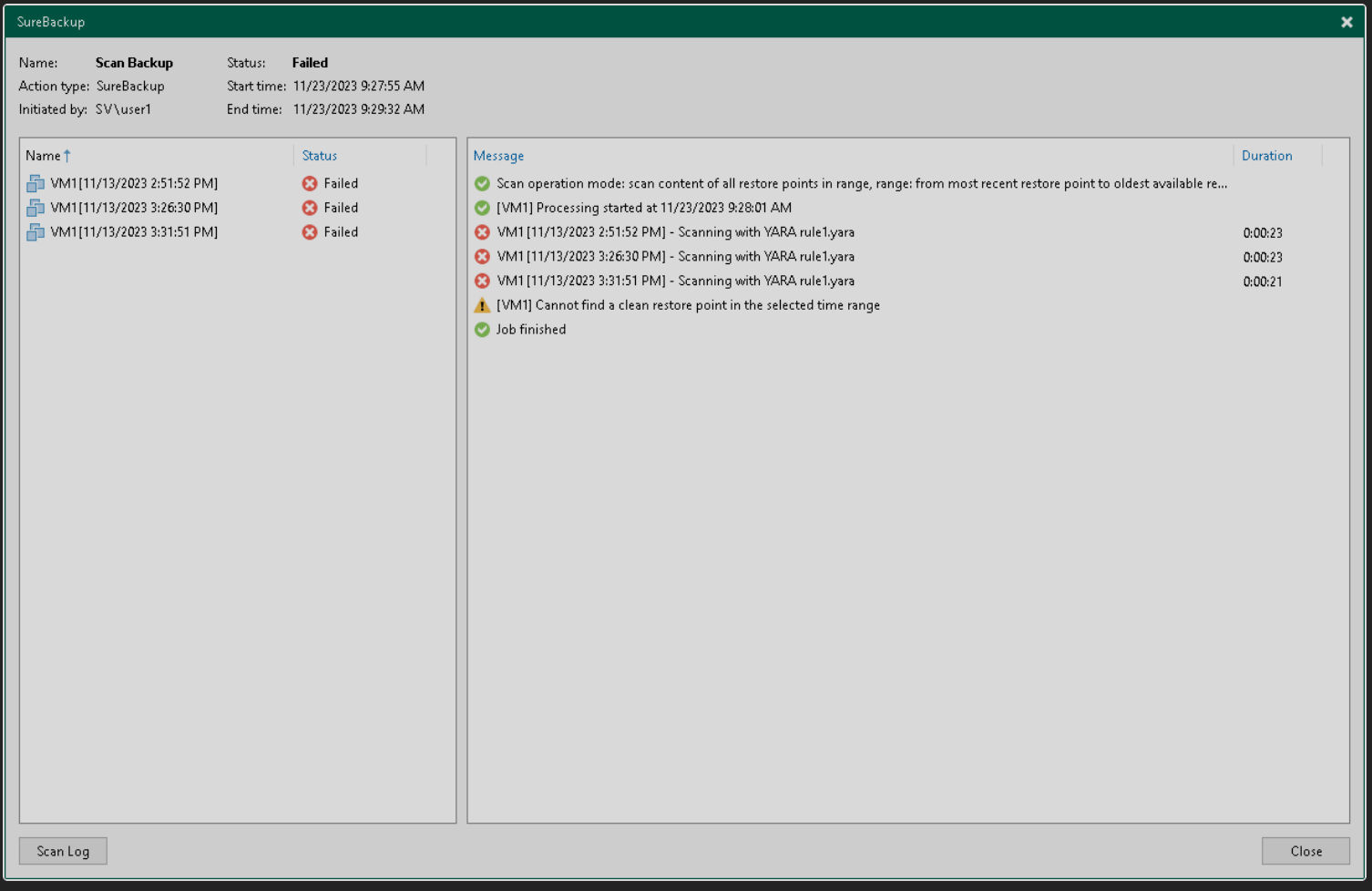
Full logs of the scan are stored on the mount server in the following folder: C:\ProgramData\Veeam\Backup\FLRSessions\Windows\FLR__<machinename>_\Antivirus.
As you can see this was just a small example of identifying files and creating YARA rules with Veeam Backup & Replication.
For more information on strings and conditions, head over to learn more: Writing YARA Rules.
Hope this information gave you a good understanding about getting started with YARA rules and how to utilize them in Veeam Backup & Replication.