Redhat’s Openshift owns a large portion of the Kubernetes market and some call it the most complete Kubernetes distribution of all.
In this post we will setup Redhat’s Code Ready Containers which is a single node developer Openshift version that will fit on your laptop.
We will perform the following steps:
1 Download and install CRC (Code Ready Containers)
2 Explore both the CLI and Web Console
To install CRC we first need to head over to the Redhat website and login with our Redhat account (you can also create a free account that will allow you to perform the download)
https://developers.redhat.com/products/codeready-containers/overview
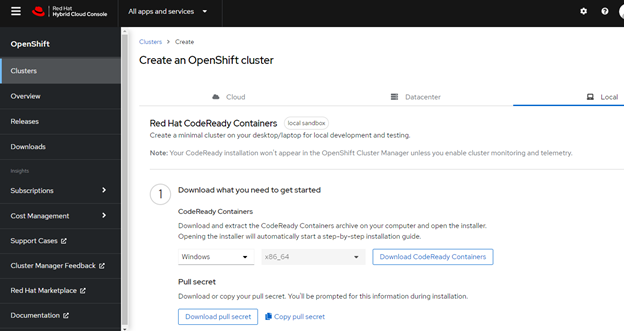
Choose your OS and make certain to also download the pull secret.
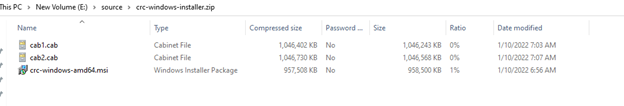
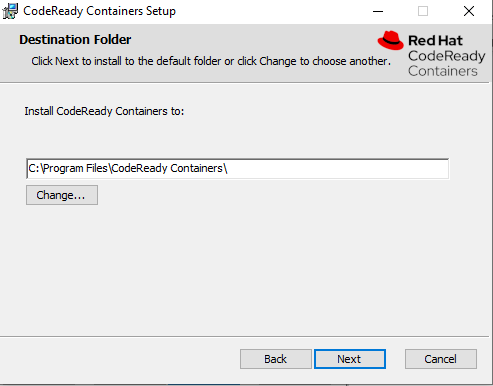
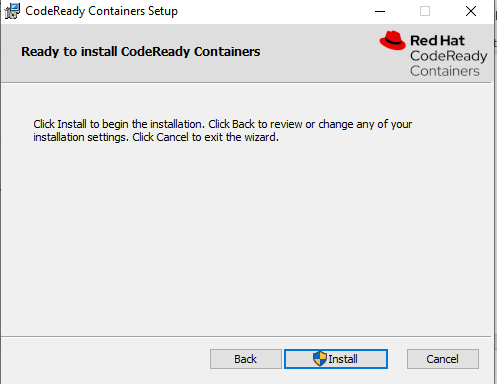
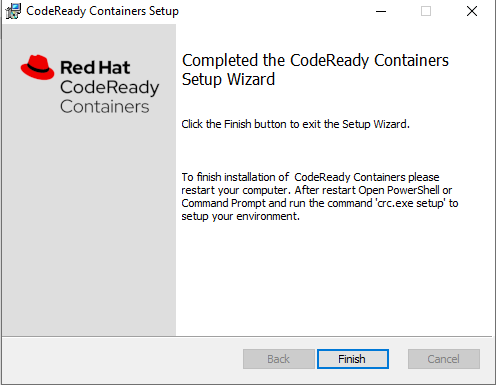
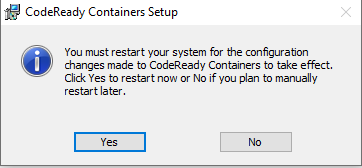
Unzip the archive and run the MSI (if you are in windows)
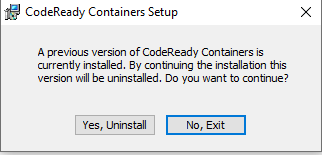
I have an older version of CRC installed and you cannot upgrade unlike in a fully licensed Openshift cluster. So the older version and everything in it will be deleted.
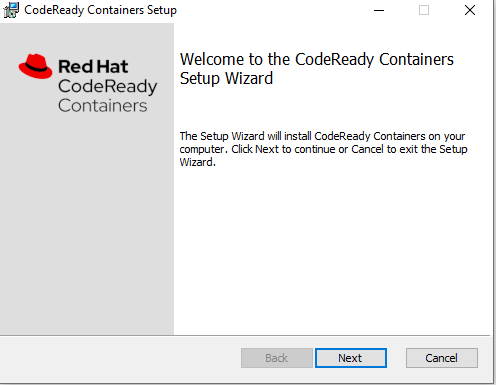
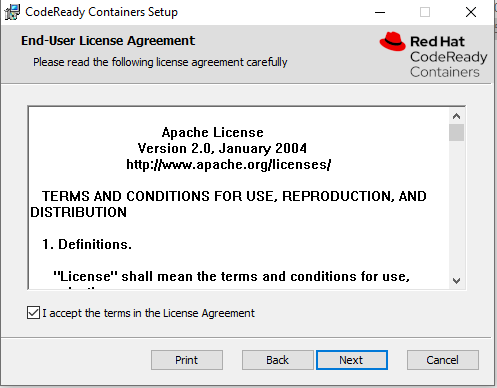
We accept the agreement (Apache License) and move along:
After rebooting your laptop you will notice the Red CRC icon in your tray.
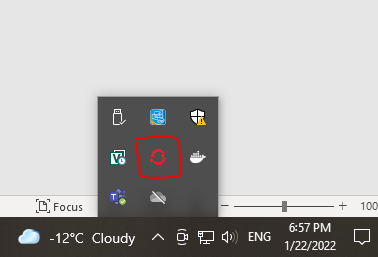
You can right click on that icon and get various options or just use the CLI.
We will use the CLI since we love the command line!
Type crc setup, you will be prompted to paste in your pull secret if this is the first time that you are deploying.
crc setupAfter this type crc start to have crc build your cluster
crc start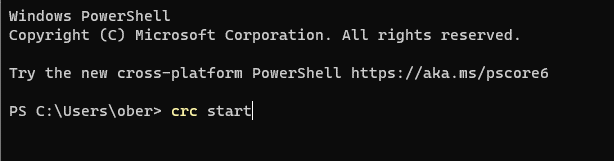
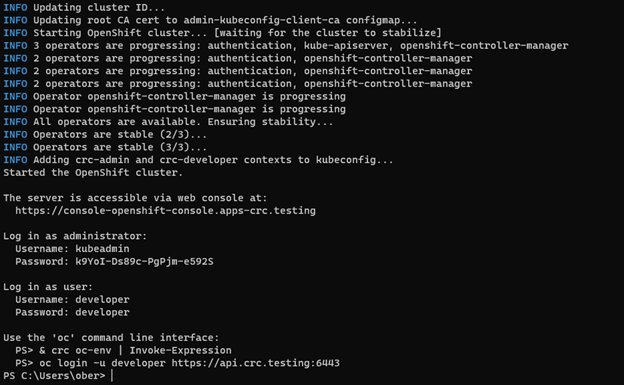
Ok the install is done. Make sure to jot down the login information and the following command to make sure your environment is ready to use oc.
& crc oc-env | Invoke-Expression
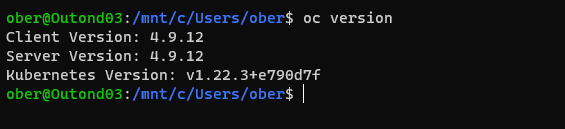
We can type oc version to make sure all is working well (for those who have installed the Windows Sybsystem for linux you can switch to bash if you wish to do so but you may need to create aliases for oc i.e. alias oc=oc.exe in your .bashrc file)
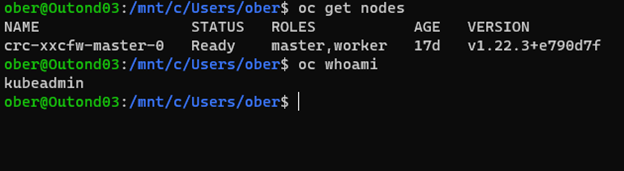
By default CRC has logged us in as kubeadmin which is the super user so we can test our setup by checking the get node command.
Oc in this case works just like kubectl
Why don’t we try out the web console.
To do this we can type crc console
crc console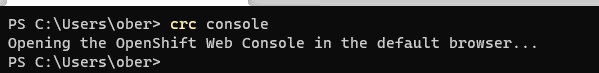
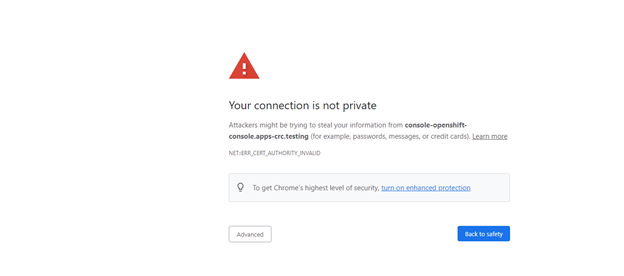
We will need to accept twice the self-signed cert
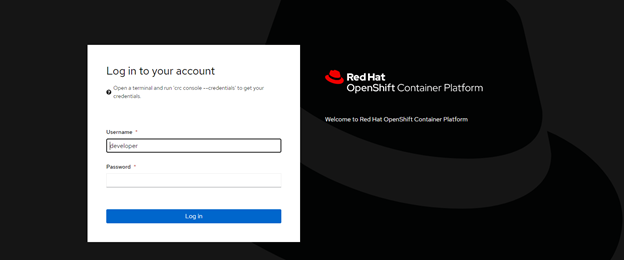
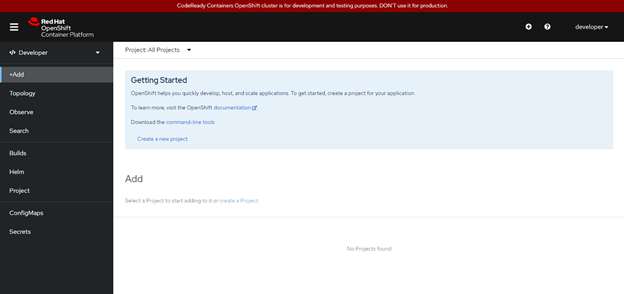
We can login as developer and see what a user with only restricted rights will see:

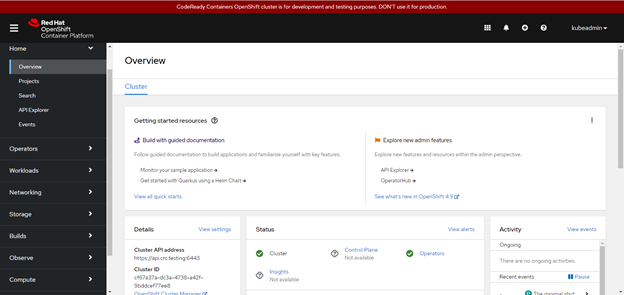
Or we can logout and log back in as kubeadmin (the password was provided on the screen when the setup program completed. Here we get a lot more options and complete vision of the entire cluster.
Redhat’s Openshift is a very mature Kubernetes distribution and we have only touched on a basic install of CRC. I hope to create more posts going forward delving deeper into this fantastic product.


