next up:
Find a setting which sets the setting as default for every repository I add (prefer to add one wasabi respotiory for each customer. Perhaps not the best solution though...) What do you guys/girls do?
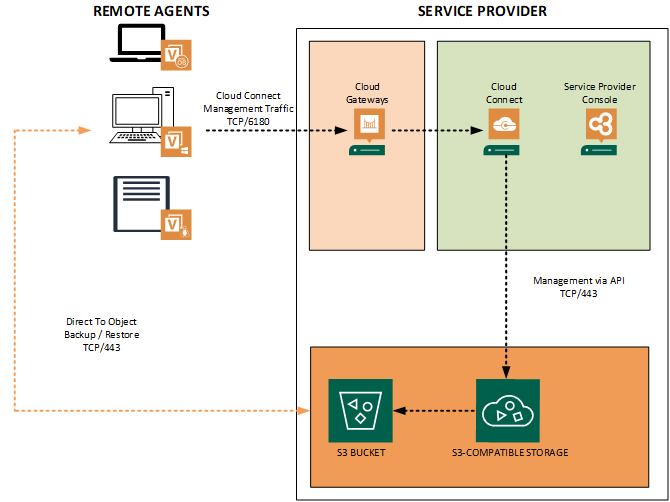
It looks like the secure mode is going to be the way to go. Somewhat related, I know that for VBR installations, it’s recommended to have a separate bucket for each backup server because otherwise you introduce performance issues because you have multiple servers trying to read/write the metadata for the bucket. In my case, I have multiple buckets under the same account. As for using the Veeam agent, it certainly doesn’t make sense to have a bucket for each agent, so I’m curious about this secure mode as well, and also to see if this could filter back into VBR where you could then have multiple servers accessing the same bucket. In most cases, I think I’d still want them separate because I can then easily see how much each bucket is consuming and bill back if needed based on usage, but then again, I have one client that has two VBR deployments - one for their main datacenter, and one for a subsidiary that they acquired, so each deployment is using a separate bucket and we have to tally the utilization for both - it could be nice to have them going to the same bucket if possible.
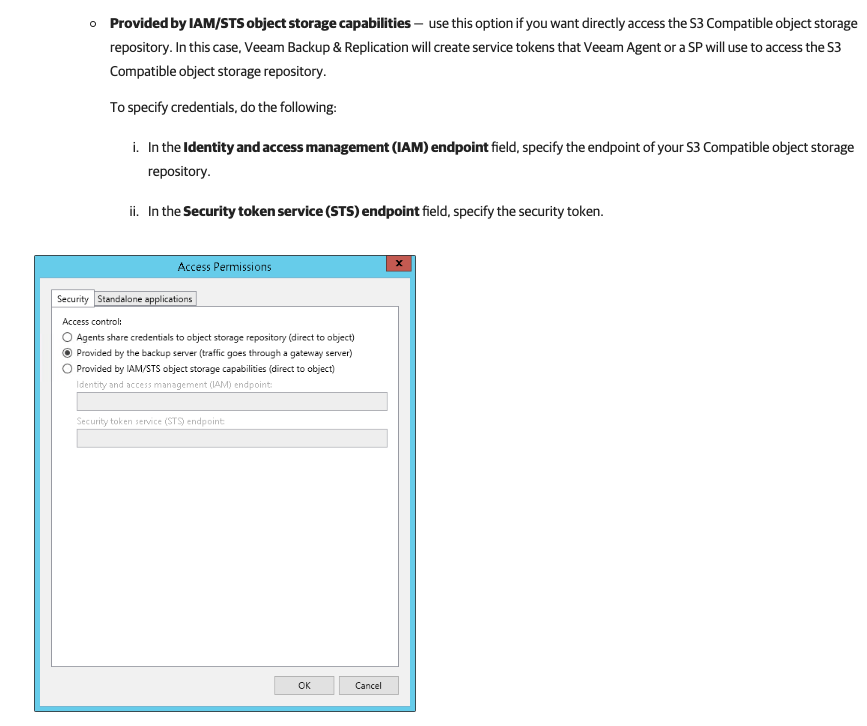
You can also send VBR backups into OBJS via Secure Mode, but in this case the tenancy will be only one, as the idea is that every vm from the same server belongs to the same tenancy. I didn’t tested the VBR scenario, but in your case as I understood there will be two STS accounts, one for each VBR; to be confirmed.
Where Secure mode shines is indeed with Agents, where the automatic creation of STS users makes a lot of sense. By the way, it works not just for S3, but also Azure and GCP, even if in different ways as the protocol is different.
About the design, I didn’t see it applied yet in the field (also cause there’s no documentation yet lol, so I hope my paper will help) but I guess that for billing/performance reason, people would indeed use one bucket for each tenant, and then use secure mode inside each tenant. I’m curious to read opinions from service providers, how do they see it fit.
PS: don’t forget block storage for VCC, as Secure Mode works only if sources is VBR v12 and its related Agents. v11 and v10 cannot use Secure mode, but still need to be supported.