Good morning everyone!
Today I’m here to share a relatively new CVE, related to Veeam Backup for Google Cloud v1.0 and v3.0, published on 5 December. Maybe someone missed it.
It has 9.8 as CVSS V3 score, so it’s a critical one.
BUT DON’T PANIC.
Continue to read to find the solution.
It’s about an improper authentication in Veeam Backup for Google Cloud v1.0 and v3.0 that allows attackers to bypass authentication mechanisms.
Veeam already published update to solve this CVE, and you just must look at the version of the product. As cited by KB4374:
For most users, no actions will be needed, as the Veeam Updater component will have automatically installed this fix during its daily check for updates. After the fix has been installed, the Backup Appliance will be restarted automatically. For environments where the Veeam Backup for Google Cloud backup appliance does not have access to repository.veeam.com, the fix will have to be manually deployed or internet access configured to allow access to the update server.
Update server: https://helpcenter.veeam.com/docs/vbgc/guide/ports.html?zoom_highlight=repository.veeam.com&ver=30
CVE link: https://nvd.nist.gov/vuln/detail/CVE-2022-43549
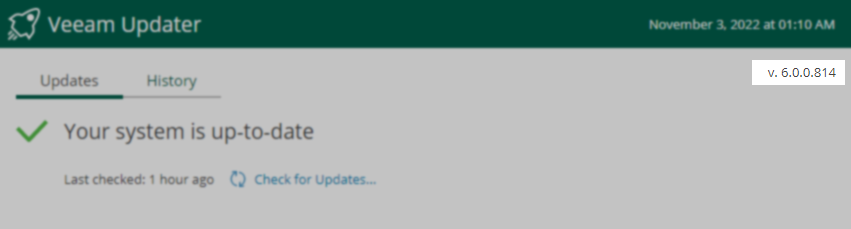
To verify version of that component it’s simple: just login in the web console. The fix for the vulnerability documented in this article is being shipped alongside Veeam Updater version 6.0.0.814 and higher.
Screen: