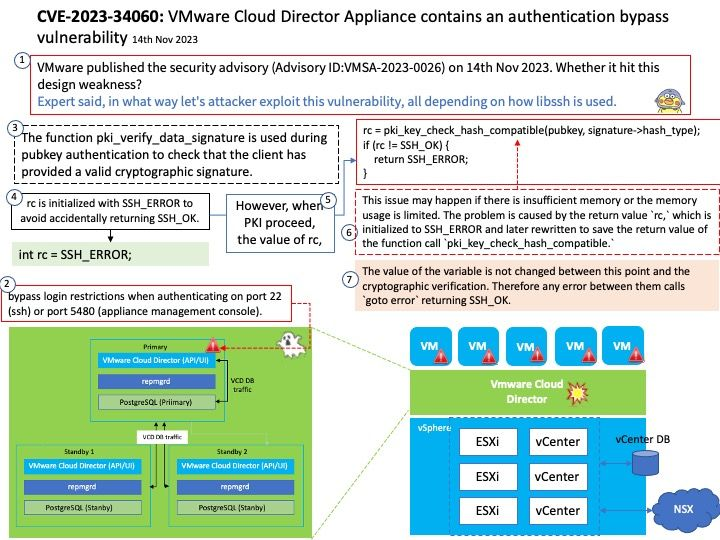
URGENT SECURITY ALERT: VMware has issued a warning about a critical and unpatched vulnerability in Cloud Director. Tracked as CVE-2023-34060 with a CVSS score of 9.8, this flaw affects instances upgraded to version 10.5 from an older version.
On an upgraded version of VMware Cloud Director Appliance 10.5, a malicious actor with network access to the appliance can bypass login restrictions when authenticating on port 22 (ssh) or port 5480 (appliance management console). This bypass is not present on port 443 (VCD provider
and tenant login). On a new installation of VMware Cloud Director Appliance 10.5, the bypass is not present.
While a fix is pending, VMware has released a shell script (https://kb.vmware.com/s/article/95534) as a workaround. This temporary mitigation won't disrupt Cloud Director installations.
More information: https://www.vmware.com/security/advisories/VMSA-2023-0026.html