Hello everyone. Last time we explored how to identify basic file Indicators of Compromise (IoCs), develop YARA rules to detect malicious actors, and incorporate these rules into Veeam Backup & Replication to identify potential malware in our backups.
Taking it a step further, today we will explore how to automatically generate YARA rules using YarGen.
YarGen
YarGen is a tool that generates YARA rules from a specified malware file. It identifies unique strings within the malware and excludes those prevalent in non-malicious files. This is achieved using YarGen's comprehensive database of strings and opcodes typically found in non-malicious files. Essentially, it creates YARA rules from strings in malware files while discarding those also present in goodware files.
There are many variable and options that can be set in YarGen, today we are going to look at how it can create a YARA rule based off of a potential malware file.
Back to basics - IoCS
A user has noticed a folder called “freestuffhere” on their system. Inside there is a file called freeiphones.txt. Much like in Part 1, we can analyze the file to identify any indicators of compromise (IoCs).
- File name: freeiphones.txt
- File path: /home/veeam/tools/yarGen/freestuffhere/freeipones.txt
- Size: 90 bytes
- Strings: “VGhpcyBpcyBub3QgdGhlIGRyb2lkIHlvdSBhcmUgbG9va2luZyBmb3Iu O66. DV. LS. #%%%^apple##promax”
- MD5 Hash: bc869ef7b6d284cd066c35842d3a3742
YarGen Setup
Now that we have the information as reference, let’s take a look at YarGen in action and let it create the YARA rule.
First thing we need to do is install YaraGen and its dependencies. I am running my demo in ubuntu, so YMMV.
Repo for yarGen: github.com/Neo23x0/yargen
git clone https://github.com/Neo23x0/yarGen.gitNow we need to install some additional components.
sudo apt install python3-pip
pip install lief
pip install lxmlThen let’s update yarGen’s database.
python yarGen.py -uNow we can run yarGen against the suspicious directory to create the YARA rule:
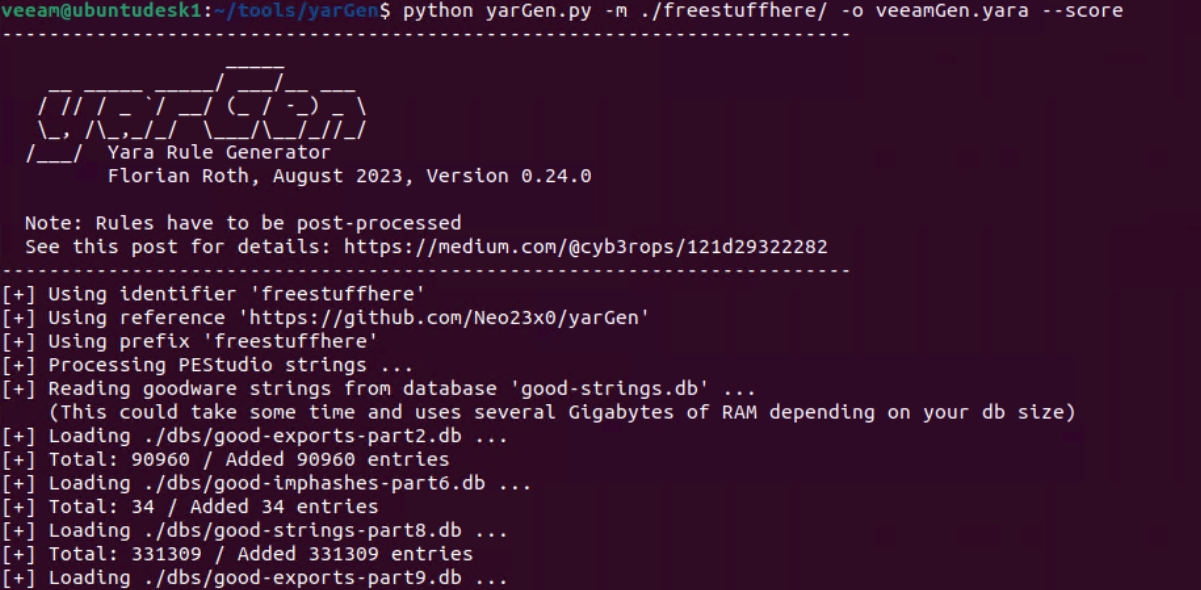
python yarGen.py -m ./freestuffhere/ -o veeamGen.yara --score(-m path to scan for malware, -o output rule file name, —score shows string scores from yarGen database)
Now let’s take a look at the YARA rule yarGen has created:
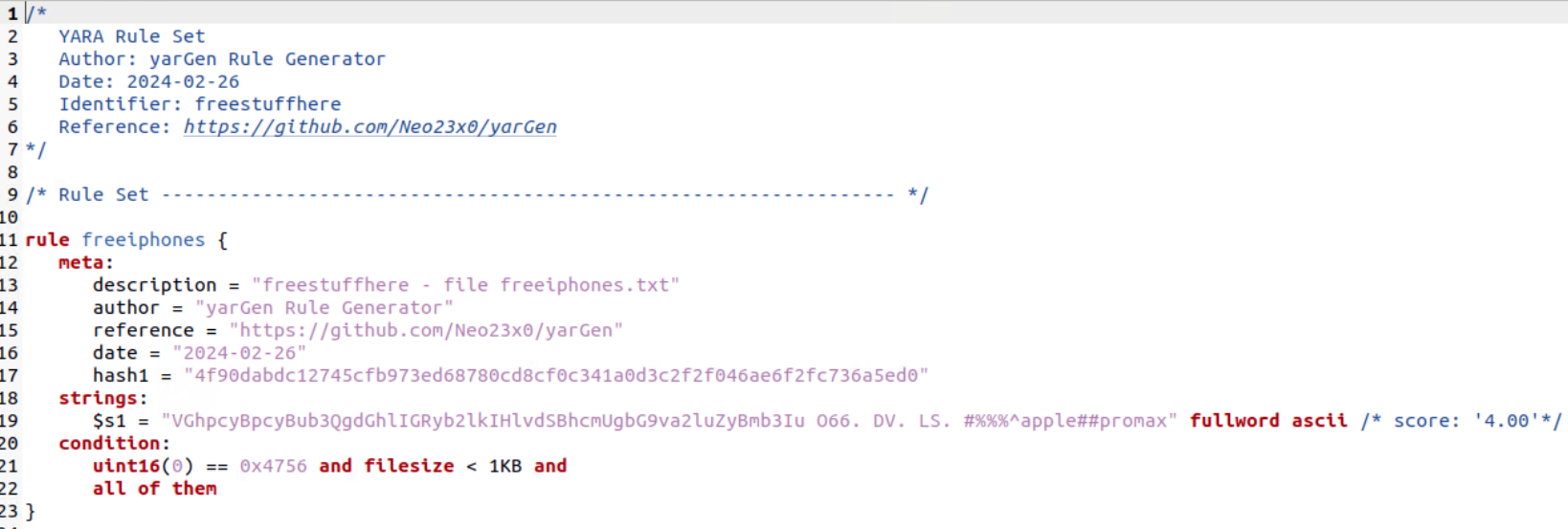
The string in the freeiphones.txt file is identified with a score of 4. If this was something else like an actual piece of malware, it may have a higher score. As previously mentioned, yarGen has many configurable options to configure, including setting minimum and maximum scores.
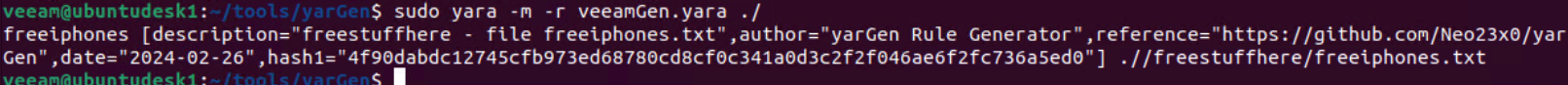
Now to validate this YARA rule let’s run it:
Well that was just an example of whats possible on creating YARA rules with yaraGen. For more information on yarGen and how deep the rabbit hole can go, check out their Github page - https://github.com/Neo23x0/yarGenhttps://github.com/Neo23x0/yarGen
