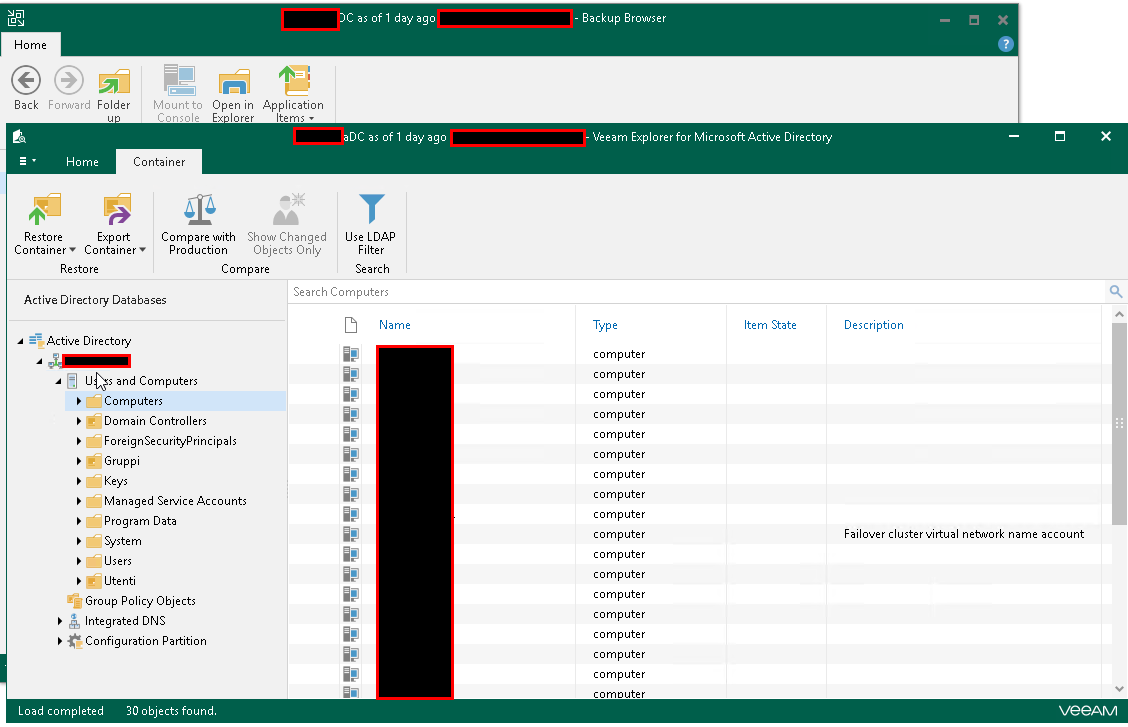
Hi all. There is the possibility that this weekend I might need to restore all of our domain controllers in our domain (hopefully this does not come to pass). It is not a very active AD domain so hopefully but I might have to go back about 3 weeks to get around a problem.
Can someone point me to documentation as to how to do this from within Veeam with all the DCs down? This would mean that no dns resolution will be happening (do I have to create a hosts file on the Veeam server to get around this?).
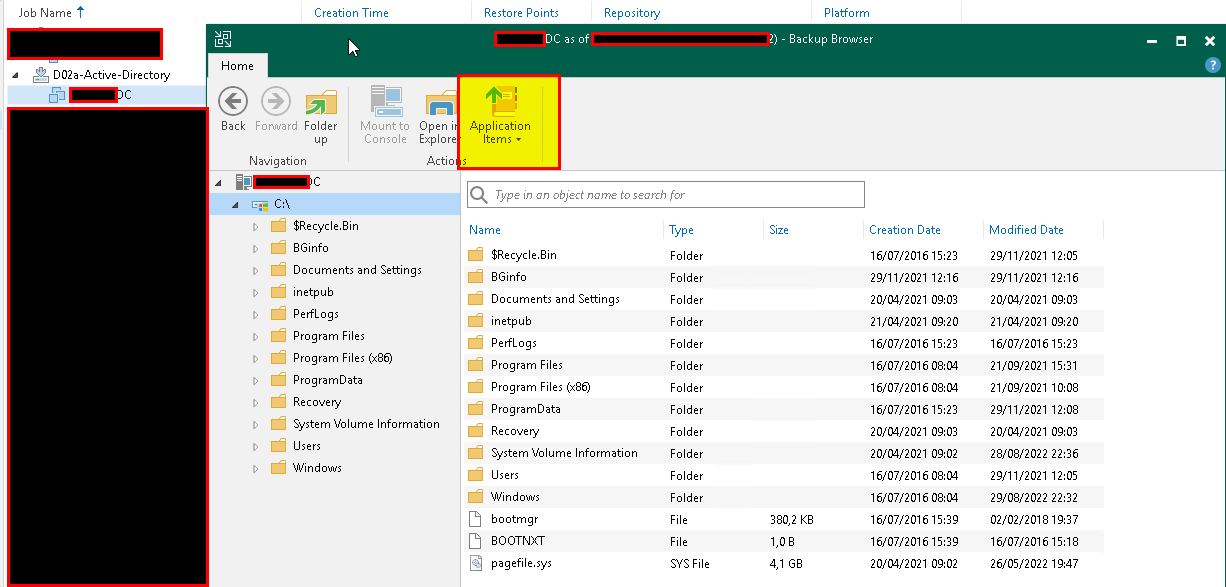
Another hiccup is that for one of the DCs, I notice now that application aware processing has not been turned on so it is going to be restored as just a member server without any special processing for the AD database.
Thanks.
Best answer by regnor
View original