Field Experience — When the Human Link Becomes the Missing Link
By a cybersecurity consultant, from the field.
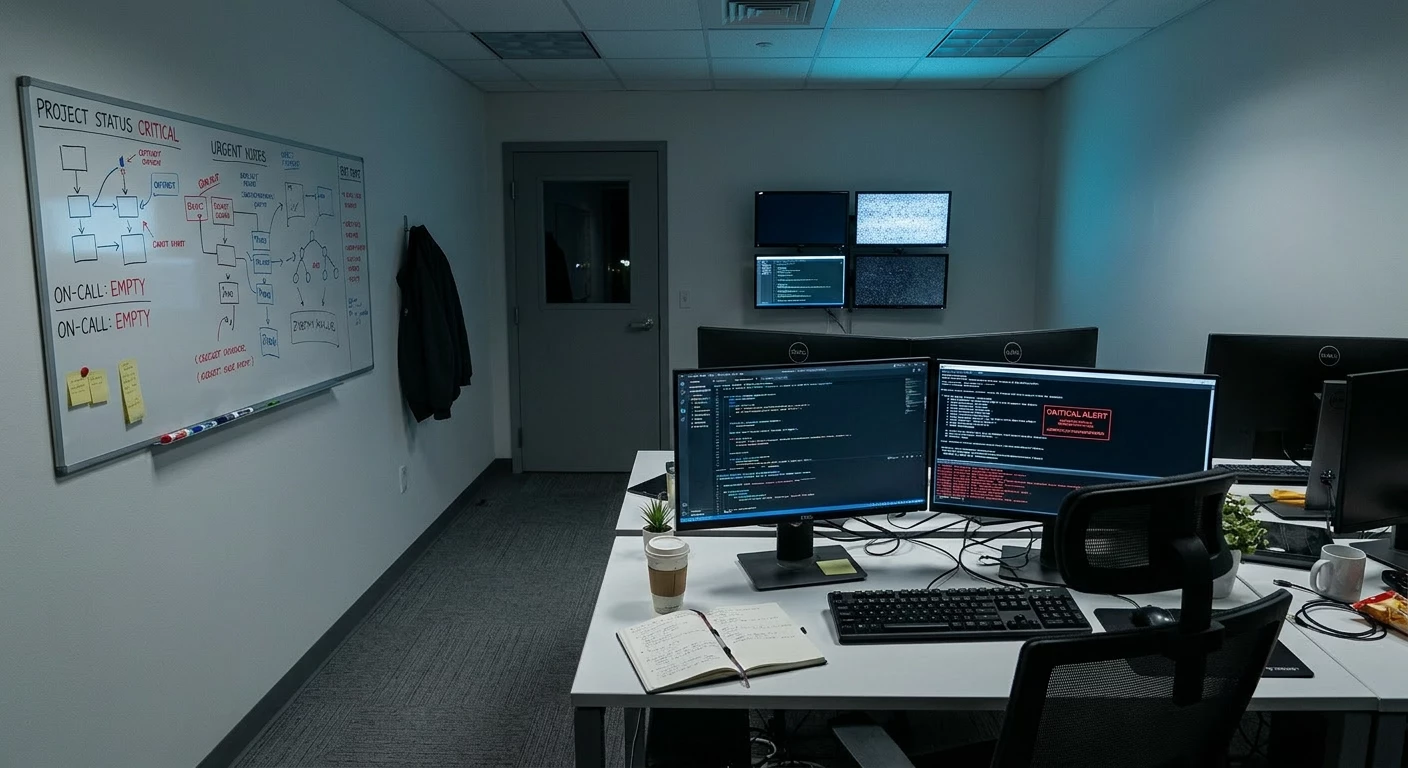
The Day Everything Stopped… Without a Cyberattack
Imagine the scene.
No ransomware. No server failure. No fire in the server room. And yet, an entire company's information system finds itself in total disarray.
The cause? Two simultaneous, extended sick leaves. The only two people who made up the internal IT department.
This is exactly the scenario I discovered when I arrived at this client's site. A scenario that nobody had anticipated, that nobody had recorded in a risk register, and which nevertheless caused an operational paralysis as severe as a major cyberattack.
A Deafening Digital Silence
Within the first few hours of my assignment, the situation was alarming:
- No more daily IT infrastructure management: no monitoring, no updates, no ticket handling.
- Zero visibility on backup status: Are the jobs still running? When did someone last check them? Are the storage media healthy? Nobody knows.
- Security alerts piling up, unread: antivirus, EDR, firewall, SIEM… dozens of notifications left unattended for weeks.
- No usable documentation: passwords, procedures, architecture diagrams — everything was "in the heads" of the two absent employees.
- And the most terrifying question: what do we do in the event of a cyber crisis right now, at this very moment?
The honest answer? Nothing. We can do nothing. We don't even know where to start.
We Back Up Data. We Test Restores. But We Forget the Most Important Thing.
The cybersecurity community has been hammering home — rightly so — three fundamental pillars for years:
1. Back Up. Everything. Regularly.
The 3-2-1 rule (three copies, two different media, one copy offsite) is now a recognised standard. Companies invest in high-performance, replicated, encrypted backup solutions. This is essential.
2. Test Your Restores. For Real.
A backup that has never been tested is not a backup — it is an unverified promise. Regular restore tests (DRP/BCP) must prove that a service can actually be rebuilt within an acceptable timeframe (RTO) and with a controlled level of data loss (RPO).
3. Document, Proceduralize, Automate.
Every technical component must be documented. Every critical process must have its procedure. Automation reduces dependence on human intervention.
All of this is necessary. None of it is sufficient on its own.
Because there is systematically a missing fourth pillar — one that almost nobody dares to question:
Who actually pushes the button?
The Human Factor: The Great Forgotten Element of Risk Analysis
Let's be honest. In the majority of small and medium-sized businesses, the IT department relies on one to three people. Sometimes just one. These employees are often:
- The sole holders of critical technical knowledge,
- The only ones authorised to access administration consoles,
- The only ones who know that the accounting server backup script fails every Tuesday and needs to be restarted manually,
- The only ones who know the domain administrator password — sometimes stored nowhere other than in their own memory.
When these people become unavailable — illness, accident, resignation, burnout, conflict, simultaneous departure — it's not just one service that stops, it's the entire digital resilience capacity of the organisation that collapses.
And yet, look through standard risk analyses. You'll find:
- ✅ Risk of fire in the server room
- ✅ Risk of ransomware cyberattack
- ✅ Risk of critical hardware failure
- ✅ Risk of prolonged network outage
- ❌ Risk of total or partial loss of IT human resources
This risk is almost systematically absent. Or, when it is mentioned, it is treated with disconcerting casualness: "The managed service provider will take over." Really? Do they have the access credentials? Do they know your infrastructure? Have they been briefed? Do they have a contractual mandate to intervene in an emergency? In most cases: no.
What This Field Experience Teaches Us
The incident I experienced at this client's site is not an isolated case. It is a representative example of a structural vulnerability that I encounter in the majority of mid-sized organisations.
Here are the lessons I draw from it — lessons I urge you to integrate immediately into your continuity strategy.
▶️ Lesson #1 — Include IT HR Risk in Your Formal Risk Analysis
The loss of IT skills must appear explicitly in your risk register, on the same level as a hardware failure or a cyberattack. Assess:
- Likelihood: sick leave, staff turnover, retirements, accidents, simultaneous departures — the probability is far higher than most people realise.
- Impact: depending on the number of people affected and their criticality level, the impact can range from service degradation to total paralysis.
- Mitigation measures: and this is where the real work begins.
▶️ Lesson #2 — Formally Map "Who Does What"
Every critical IT function must be identified and assigned to at least two people capable of performing it:
| Critical Function | Primary | Internal Backup | External Backup | Associated Documentation |
|---|---|---|---|---|
| Backup administration | Person A | Person B | Provider X | Procedure BAK-001 |
| Security monitoring / alerts | Person A | Person B | Outsourced SOC Y | Procedure SEC-001 |
| Access management / Active Directory | Person B | Person A | Provider X | Procedure IAM-001 |
| Cyber crisis management | Person A + Management | External CISO | CERT Provider Z | Crisis Plan CRI-001 |
If any cell in this table is empty, you have identified a critical vulnerability. Treat it as such.
▶️ Lesson #3 — Create a "Human Plan B" for Every IT Resource Loss Scenario
Beyond the technical disaster recovery plan, you need a human DRP:
- Scenario 1 — Partial loss (one person out of two or three unavailable): who takes over their responsibilities? With what access? Within what timeframe?
- Scenario 2 — Total temporary loss (the entire IT team simultaneously unavailable): which external provider steps in? With what contractual response time (SLA)? With what pre-provisioned access?
- Scenario 3 — Total permanent loss (simultaneous resignations, restructuring): what is the emergency recruitment plan? What documentation enables a new arrival to become operational?
Each of these scenarios must be documented, communicated to senior management, and tested at least once a year.
▶️ Lesson #4 — A Digital Vault Is Not a Luxury, It Is a Vital Necessity
All of the following must be stored in a secure digital vault, accessible by at least two trusted individuals (including one outside the IT department — typically a member of senior management):
- Passwords for all administrator accounts (local, domain, cloud, backups, firewalls…)
- Network and systems architecture diagrams
- An up-to-date inventory of hardware and software assets
- Step-by-step restore procedures
- Contact details for critical providers, including contract numbers and support access codes
- Backup encryption keys
If your system administrator is the only person who knows the decryption password for your backups, those backups no longer belong to you. They belong to them.
▶️ Lesson #5 — Contractualise an External Safety Net
Even if you have an internal IT team, an on-call or fallback contract with an external provider is essential to cover the IT HR loss risk:
- Emergency IT support contract with defined SLAs (response within 4, 8, or 24 hours)
- Pre-provisioned access: the provider must have the necessary access in advance (VPN, dedicated administration accounts, documentation), stored securely and activatable on trigger
- Annual onboarding exercise: the provider must prove they are capable of taking over critical operations in a real situation
A contract gathering dust in a drawer that has never been activated is as reliable as a backup that has never been tested.
▶️Lesson #6 — Test the Absence Scenario, Not Just the Failure Scenario
You are probably already testing your backup restores (and if not, stop reading this article and schedule a test immediately). But are you testing the following scenario?
"Our IT manager has been unreachable for 48 hours. A security incident has just been detected. What do we do, concretely, in the next 30 minutes?"
If nobody in your organisation can answer this question operationally, you are in a critically vulnerable position.
Integrate this scenario into your crisis exercises. Have it played out by people outside the IT department. Measure the response times. Identify the bottlenecks. Fix them.
A Necessary Paradigm Shift
What this field experience reveals is a deeply ingrained cognitive bias in our approach to IT resilience: we think in terms of machines, software, networks and data. We forget that behind every critical system, there is a person who knows it, maintains it, monitors it and fixes it.
That person is not an interchangeable component. They carry within them a tacit knowledge — those dozens of micro-adjustments, workarounds and infrastructure quirks that appear in no documentation because "it would take too long to write down" or "it's obvious to anyone in the field."
When that person disappears — even temporarily — that knowledge disappears with them.
Immediate Action Plan: 10 Questions to Ask First Thing Monday Morning
If this article resonates with you, start by asking these ten questions within your organisation. If you cannot answer more than three of them with certainty, you have a priority workstream to open:
- ☐ How many people make up our IT department and what is the coverage rate for each critical function?
- ☐ Is there an identified and trained backup person for every critical IT role?
- ☐ Are administrator passwords stored in a vault accessible in an emergency by someone outside the IT team?
- ☐ Is our infrastructure documentation up to date, complete and usable by a third party?
- ☐ Do we have an activatable external support contract in the event of total IT team unavailability?
- ☐ Does this external provider have pre-provisioned access and knowledge of our environment?
- ☐ Have we tested an IT HR loss scenario in our crisis exercises?
- ☐ Can our backups be restored by someone other than the person who configured them?
- ☐ Does the IT HR loss risk appear in our risk register with a treatment plan?
- ☐ Is senior management aware of and involved in addressing this risk?
Conclusion: Resilience Is Human Before It Is Technical
We invest thousands of pounds in redundant backup solutions, next-generation firewalls, sophisticated EDR platforms and meticulously documented disaster recovery plans.
Yet we allow the entire ecosystem to rest on the shoulders of one or two people — with no Plan B, no documentation, no safety net.
It is like installing a state-of-the-art alarm system in a building and entrusting the only key to a single person — no spare, no emergency code, no backup guard.
The most critical backup in your infrastructure is not the one protecting your servers. It is the one protecting the human expertise that keeps them running.
Protect it with the same rigour.
This article is based on a real field experience.




