Hi Everyone,
Vulnerabilities wait for no-one, so whilst some are enjoying a weekend off, others are patching to protect against the latest risk. Log4j.
This post has two objectives. Firstly I’m sharing my write up regarding the issues I’m aware DO have an impact to VMware, secondly what does this mean to the Veeam products…
First up: VMware
I don’t often dedicate a blog post to a particular security vulnerability, but since it has scored a perfect 10 CVE rating, it’s important to be aware ASAP.
VMware have identified multiple products that utilise the Apache technology that are vulnerable to the Log4j vulnerability.
What is this “Log4j” vulnerability?
A Remote Code Execution (RCE) has been discovered in Apache’s Log4j Java Library. It is possible to insert maliciously crafted strings into fields that will be logged, which then leverages the “message lookup substitution” function of Log4j to execute code. This can be used to deploy and execute payloads, or execute commands at a heightened privilege level.
This is trivial to reproduce now the vulnerability has been confirmed to exist, hence the high score. This vulnerability isn’t exclusive to VMware.
What can I do?
Firstly, keep an eye on this VMware page for the latest updates and patch your systems as updates become available. It’s also a good idea to firewall your systems to prevent unauthorised access to limit any attack footprint. But restricting the footprint is of no substitute for a patch.
Finally, if you’re one of those people living on the edge with an externally accessible vCenter, odds are good you’ve already been compromised, get it off the internet now and check!
Second, What about Veeam?
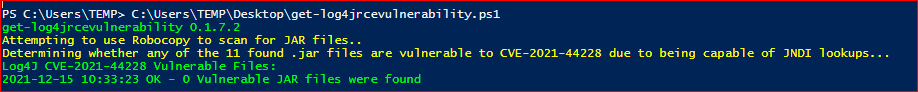
I posted on the Veeam R&D forum this morning regarding Veeam’s vulnerability status regarding this, and thankfully it appears Apache isn’t used by any Veeam product, however the Veeam security team are still investigating.
I’ll cross-post any important updates but you can see the thread yourself here.
Hopefully Veeam won’t be impacted by this one as it’s honestly one of the scarier vulnerabilities I’ve ever seen due to how widespread this is.
Finally, a shout-out to
—UPDATE—
Veeam have confirmed via the R&D forum and via a KB that none of their products are impacted (thanks