Hi all,
a new 0Day vulnerability for Windows 10 clients has been released, the article also recommends deleting all the vss restore points and recreating them
Security Update Guide - Loading - Microsoft
Check Windows 10 for SeriousSAM and HiveNightmare Vulnerability Fix - Virtualization Howto
https://github.com/GossiTheDog/HiveNightmare
commad check : icacls c:\windows\system32\config\sam
Workarounds
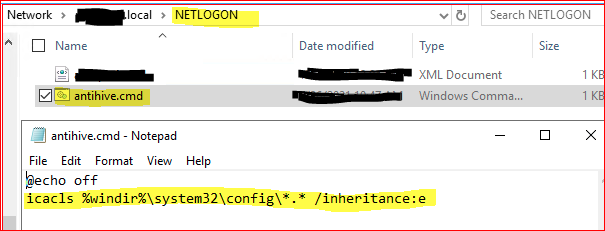
Restrict access to the contents of %windir%\system32\config
Command Prompt (Run as administrator): icacls %windir%\system32\config\*.* /inheritance:e
Windows PowerShell (Run as administrator): icacls $env:windir\system32\config\*.* /inheritance:e
Delete Volume Shadow Copy Service (VSS) shadow copies
- Delete any System Restore points and Shadow volumes that existed prior to restricting access to %windir%\system32\config.
- Create a new System Restore point (if desired).
Impact of workaround Deleting shadow copies could impact restore operations, including the ability to restore data with third-party backup applications. For more information on how to delete shadow copies, see KB5005357- Delete Volume Shadow Copies.
Note You must restrict access and delete shadow copies to prevent exploitation of this vulnerability.
KB5005357- Eliminare copie shadow del volume (microsoft.com)
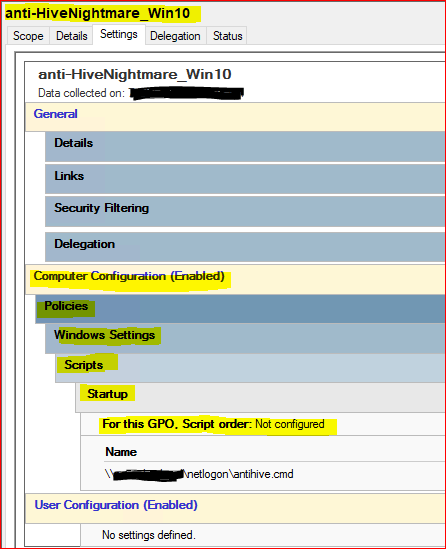
To mitigate this type of bug it is possible to use a GPO to distribute the workaround on the whole in Forest \ Domain