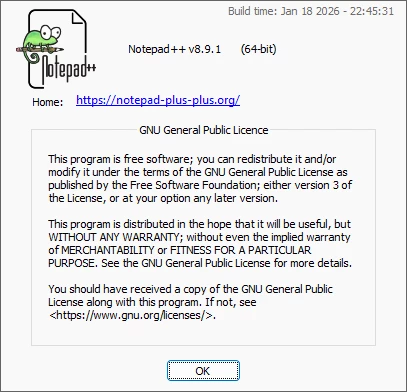
This is not good news for the large number of people who love to use Notepad++
When I was running production Veeam environments it was my go to text editor for logs, notes and various other activities.
It would seem a state actor was able through a 3rd party to gain access and after June 2025 until November the activity occured.
Read more here:
https://thehackernews.com/2026/02/notepad-official-update-mechanism.html