A couple weeks ago I had the opportunity to attend and present at the Atlantic Security Conference (ATLSECCON) in Halifax, Nova Scotia. Established in 2011, this information security conference focuses on fostering innovation, strengthening collaboration and building resilience. The conference agenda centers on everything security related; challenges, complexity and emerging threats. This was not my first time attending ATLSECCON, I have had different working roles at the event throughout the years, meaning I’ve worked booth operations, I’ve presented at the event, and I probably have coordinated just the sponsorship opportunity in the past. I am unsure of the exact number of times I have attended, but I can say I look forward to this event every year, and it only gets better over time!

After I got back, I was thinking about all the sessions I attended and some key takeaways. When I attend conferences, I really focus on what I can learn and bring with me into my everyday work. Two key elements remained with me after the conference and they were:
- Data Integrity and Trust Challenges
- AI and Agentic AI Security Risks
Throughout this blog post I will discuss some of the things I learned when it comes to these security topics as well as adding some information about the content that I had the opportunity to present.
Data Integrity and Trust Challenges
The conference opened with an interesting keynote by Wendy Nather that discussed the changes occurring in the security landscape along with the introduction of AI into the workplace and its associated risks. She highlighted data integrity, data chemistry and the need to prepare for the next wave of security attacks. The questions poised to the audience were:
- Can we trust our data?
- Do we know it wasn’t tampered with?
With data being critical to business operations, it’s important that we consider dangerous implications that can happen to it such as fake news, data misuse, and integrity attacks. One example that stuck with me was the problem of a threat actor breaking into an environment and changing data, this could be data that needs to be stored for compliance, regulatory requirements or other reasons. Having someone change just even a single line of this data could have detrimental effects on an organization’s credibility. To combat this, we need to have tools in place to monitor and log changes, providing visibility into what, when, and how data has been modified.
Another example given brought into context was data shared between different colleagues inside or outside an organization to perform tasks. Can we trust the data or validate the data we get from different departments or organizations? As the keynote made clear, if we can’t trust the integrity of our data, everything built on top of it including decisions, compliance, and operations is at risk.
AI and Agentic AI Security Risks
If you have attended any conference or presentation recently, you probably know that AI and Agentic AI are hot topics. These technologies are growing in implementations and importance across organizations. However, with all the benefits AI and Agentic AI have, there are associated security risks and challenges. I attended a few sessions on this topic, one being “Your AI Agents Are Lying to You” presented by Jason Kreistead and another “AI Security: Nailing Jelly to The Wall” by Dave Lewis.
These sessions discussed the importance of having visibility into what AI is being used in your workplace. Many organizations may not be aware of what agents are running, how they are being used, and the data they are accessing. To make this more difficult, companies cannot govern or secure what they don’t know exists. The need to establish a system of monitoring what agents are running and what they have access to is of ever-ending importance.
Agents represent a new attack surface for threat actors. Authentication for AI agents involves granting them access to systems, applications, or services on behalf of the user. Common methods of authentication such as API tokens, OAuth Protocols, embedded credentials, session cookies can all be exploited if not properly managed, giving attackers the same level of access as the agents themselves. This leads us to ask important questions; do we know every agent running in our environment? Can we see what the agents are doing during runtime and what data they accessed? As agents can act as rootkits sitting on our endpoints, where traditional monitoring may not fit. Monitoring AI agents requires something different; we need to watch their reasoning and tool calls.
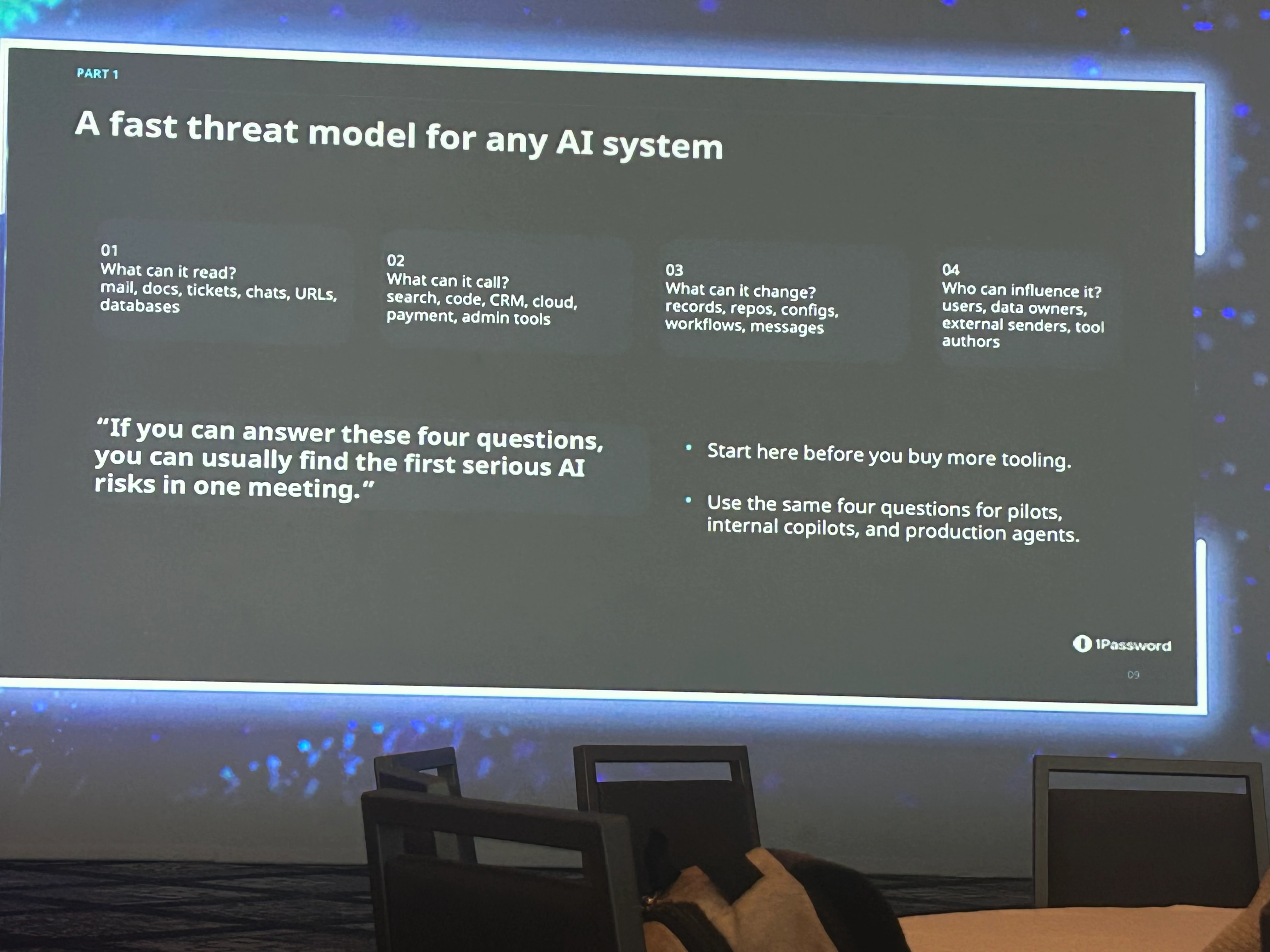
When AI agents fail, they don’t crash, they confidentially take another action to complete the task. This tells us that the failure mode for agents isn’t crash, its unauthorized behavior that looks normal on the surface. When monitoring, we need to consider policy instead of uptime, having guardrails to ensure the agent is operating in the rules we set for it, only accessing the data it’s allowed to, and lastly only taking actions that align with the organizational policy.
Data Protection Done Right: Security Strategies to Prevent Backdoors
Lastly, I was given the opportunity to deliver a presentation at the conference with my colleague
One interesting data point we discussed can be seen in this slide we presented below.
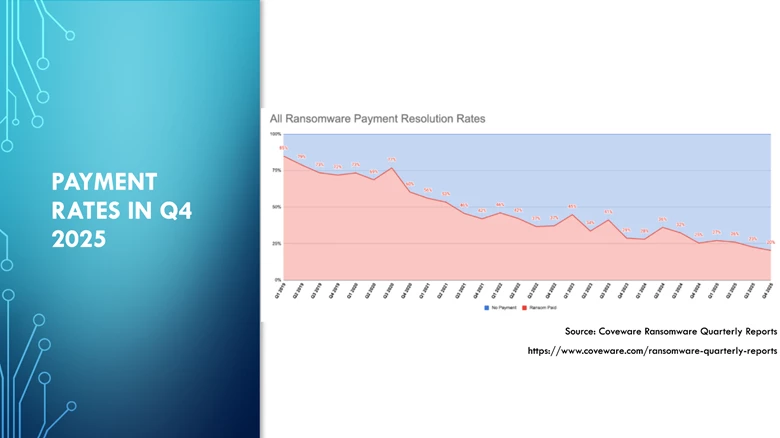
As you can see, payment rates are declining, meaning organizations are choosing not to pay despite escalating threats. This can contribute to the combined effort of organizations improved prevention, reduced blast radius or having an more established disciplined response. By having a strong data protection strategy and security controls in place, organizations can be more prepared to not pay the ransom.
What are some key aspects of a strong data protection strategy? First is understanding that backups are a part of the attack surface, they need to be secured like production. If attackers can modify or restore your backups, your recovery strategy becomes a liability. Following the 3-2-1 rule and having a copy of your data that is offline, air-gapped or immutable can be extremely beneficial when it comes to recovering.
Second, modern attacks don’t just break in, they log in. Credentials, roles, APIs, and restore operations are now primary intrusion and exfiltration paths. Zero trust must extend through backup and recovery workflows.
Lastly, being resilient isn’t just about having backups, it’s about proving you can recover. Immutable, isolated copies are essential, but they are not enough on their own. Continuous verification, least-privilege access and practiced recovery are what turn backups into true resilience.
Closing thoughts from Atlantic Security Conference
ATLSECCON reinforced a few themes that keep showing up across the security landscape. First is identity and data integrity challenges. Identity compromise is consistently the most common initial access method. This means identity and trust need to be continuously earned and validated. A Zero Trust architecture and following the principle of least privilege can reduce risk and improve security. Next, is Data Integrity, can we trust our data, and can we prove that it hasn’t been changed. Lastly, we have AI and Agentic Systems expanding the attack surface. These systems need to have visibility, governance and monitoring to better see what data they have access to. We need to have policies in place to safeguard what AI, and agents have access to and what tasks they can perform.
To combat these factors, we need to embrace resilience. Resilience is about understanding and reducing where risk lives. Applying this to our overall cybersecurity strategy, we need to make sure we not only secure our backup systems, but we can recover cleanly after an attack. Following the 3-2-1-1-0 rule, implementing a Zero Trust architecture, and verifying recovery are just some steps we can implement to reduce risk. This will help improve response readiness and provide demonstratable and repeatable resilience.

One thing I enjoy about my job is I attend these conferences, participate in them and take away key learnings. If you are ever able to attend this one, especially if you are located on the east coast, it’s an insightful experience.
What do you think of some of these key themes?



