It is being found that the official app used in installing SteelSeries devices on Windows 10 can be exploited to grant Admin rights as discovered by some security research “Lawrence Amer“. As stated by BleepingComputers, the bug can be leveraged during the device startup process using a link in the License Agreement screen that is opened with SYSTEM privileges. A real SteelSeries device is not necessary to exploit the bug. Also, a bug was discovered in the Razer Synapse software that granted unauthorised admin access. Now, a similar bug was found in SteelSeries software that gives anyone who plugs in a device complete control over a Windows 10 PC with admin rights.
Emulating a device also works: This discovery became known after news broke out about the Razer Synapse software as it was able to grant administrative privileges when connecting a Razer mouse or keyboard. This motivated the research from Jorhat, offensive security researcher Lawrence Amer (research team leader at 0xsp) found that the same can be achieved with the SteelSeries device installation software. Playing with a recently acquired SteelSeries keyboard on Monday, the researcher discovered a privilege escalation vulnerability that allowed him to run the Command Prompt in Windows 10 with admin privileges.
A real SteelSeries device is not necessary for this attack to work. Penetration testing researcher István Tóth published an open-source script that can mimic human interface devices (HID) on an Android phone, specifically for testing local privilege escalation (LPE) scenarios. After Amer published his research, Tóth published a video demonstrating that LPE discovered by Amer can be achieved using his USB Gadget Generator Tool. Here is a link to the video.
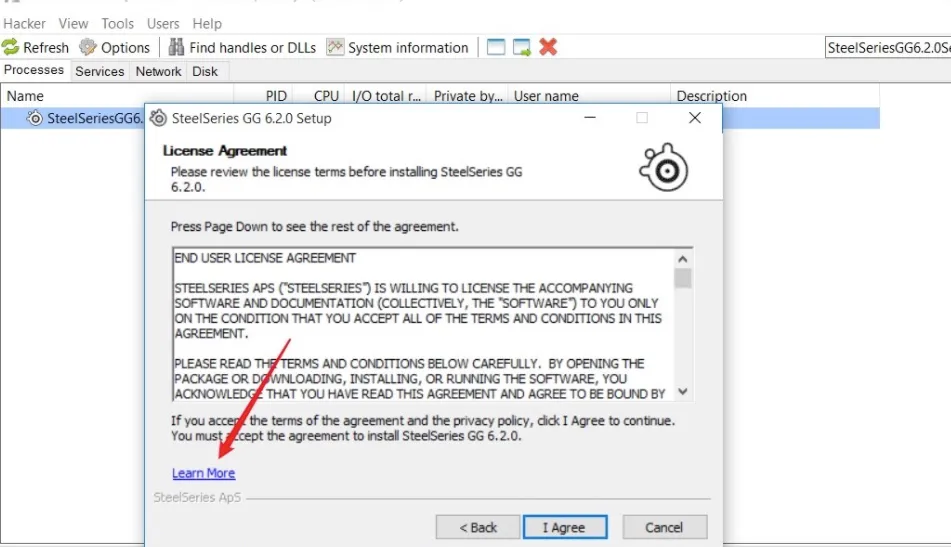
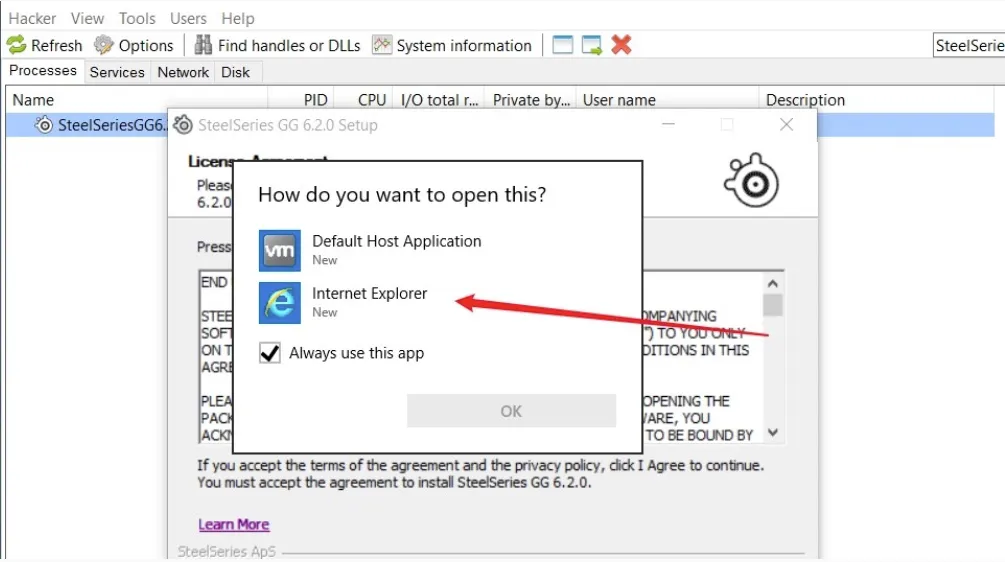
Finding the right context: While searching for the vulnerability, the researcher found a link about the License Agreement appeared with a link to SteelSeries’ privacy policy. When clicked on, the dialog for choosing a launching app appeared. Amer tested the scenario in a virtual machine that did not have file associations defined. The only process available for opening the link was Internet Explorer, which spawned as SYSTEM.
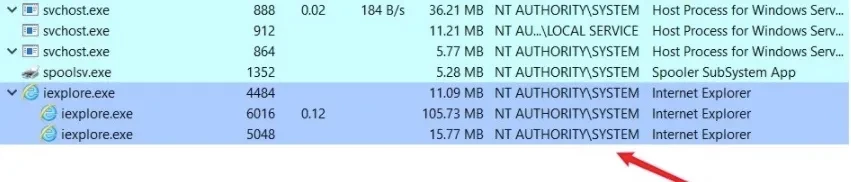
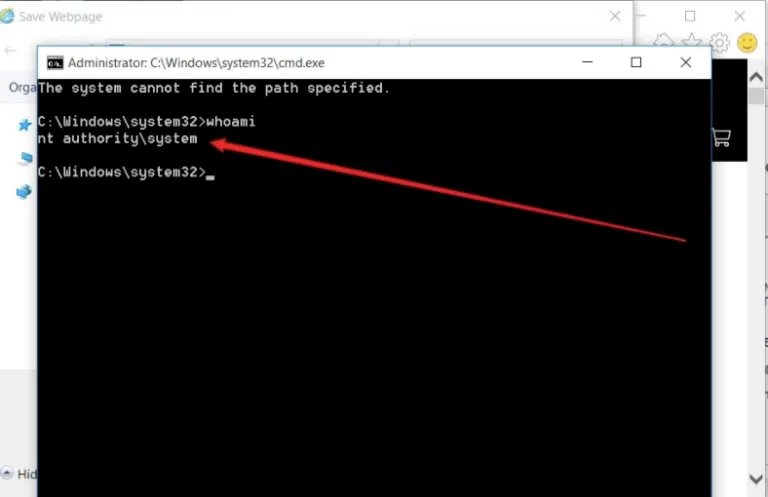
Henceforth, it was effortless to use IE to save the web page and launch an elevated privileges Command Prompt from the right-click menu of the “Save As” dialog as shown in the image below.
A SteelSeries representative talked to BleepingComputer saying “We are aware of the issue identified and have proactively disabled the launch of the SteelSeries installer that is triggered when a new SteelSeries device is plugged in. This immediately removes the opportunity for an exploit and we are working on a software update that will address the issue permanently and be released soon.” This means the exploit has been remediated for the time being.



